Threat Detection & Incident Response
Your Ultimate Defense Strategy
In today’s interconnected world, businesses are more exposed than ever to a vast array of cyber threats. From malware to ransomware, phishing to DDoS attacks, organizations constantly grapple with the challenge of identifying and responding to threats in real time. Failure to do so can result in data breaches, financial losses, damaged reputation, and regulatory fines.

Threat Detection and Incident Response Done Right
At Graylog, we’ve developed comprehensive solutions to help you combat threat detection and incident response challenges head-on. Our threat detection and incident response methodology covers the following:
Attack Surface Monitoring
Anomaly Detection
Alert Validation
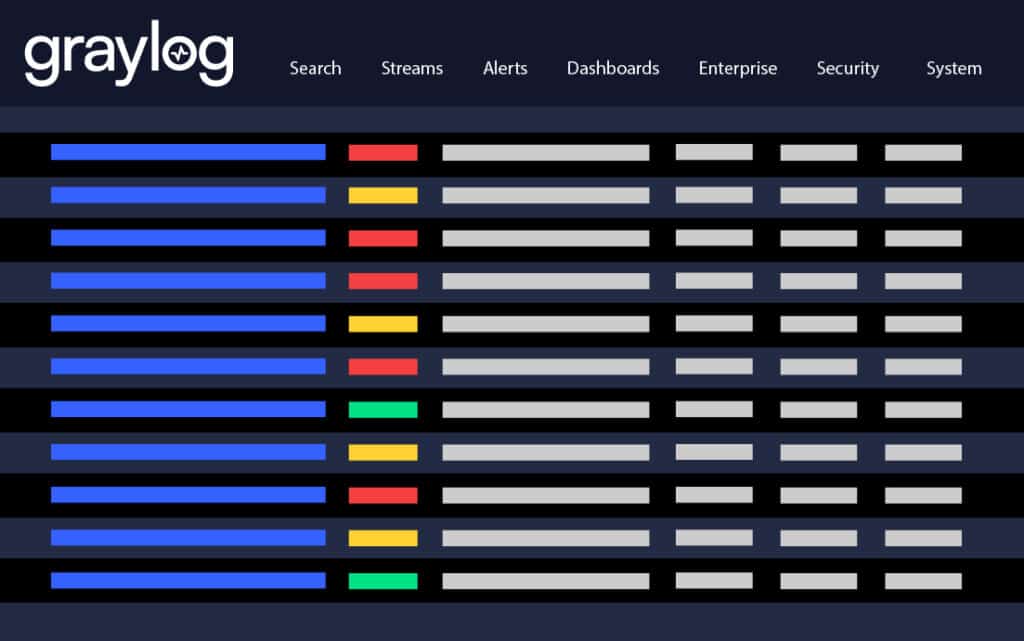
Threat Analysis and Prioritization
Incident Investigation
Incident Response and Recovery
Graylog Security: Your Security Command Center
Graylog Security can aggregate and analyze log data from various log sources and provide a centralized view of your security posture. Graylog Security can automatically detect anomalies and generate alerts for suspicious activity by correlating events from different systems across your IT environment.
Proactive Threat Detection
Graylog Security’s real-time monitoring ensures that threats are detected early, often before they can cause significant damage.
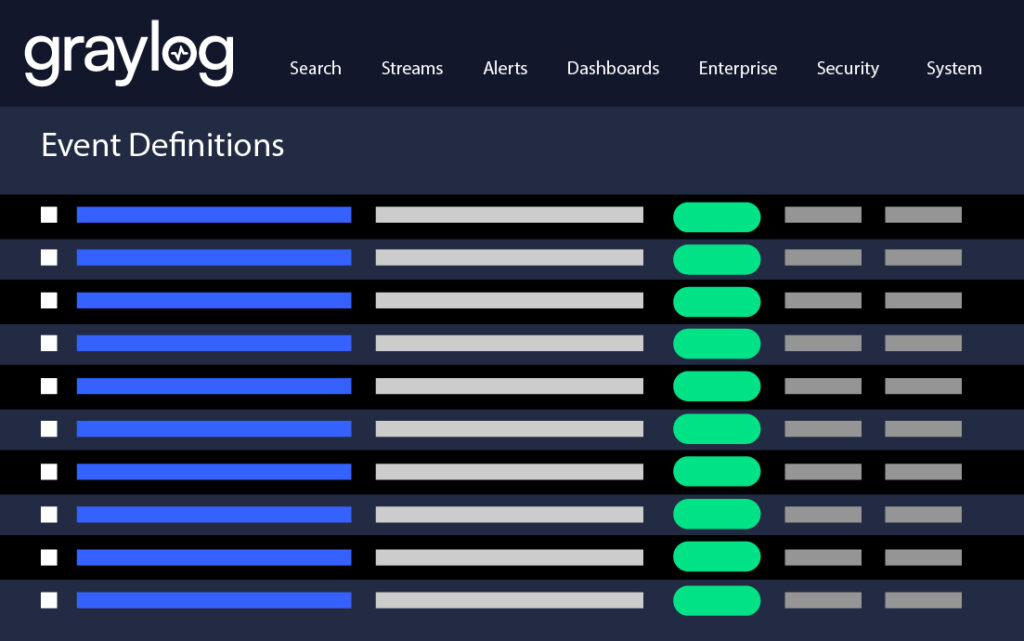
Informed Incident Response
With all relevant threat data centralized in Graylog Security, your security teams can swiftly investigate, respond to, and mitigate incidents, minimizing potential damage.
"One of the best SIEM tools — log aggregation, quick searching, flexible configuration, easy to set up, able to process large amount of data, fast."
- Software Development Engineer in Biotech Industry
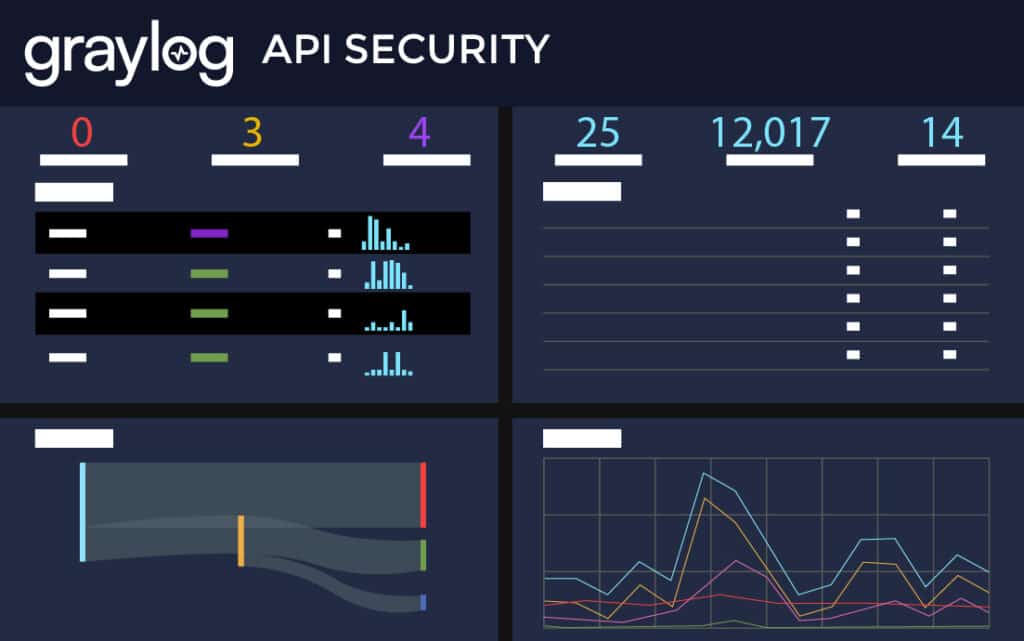
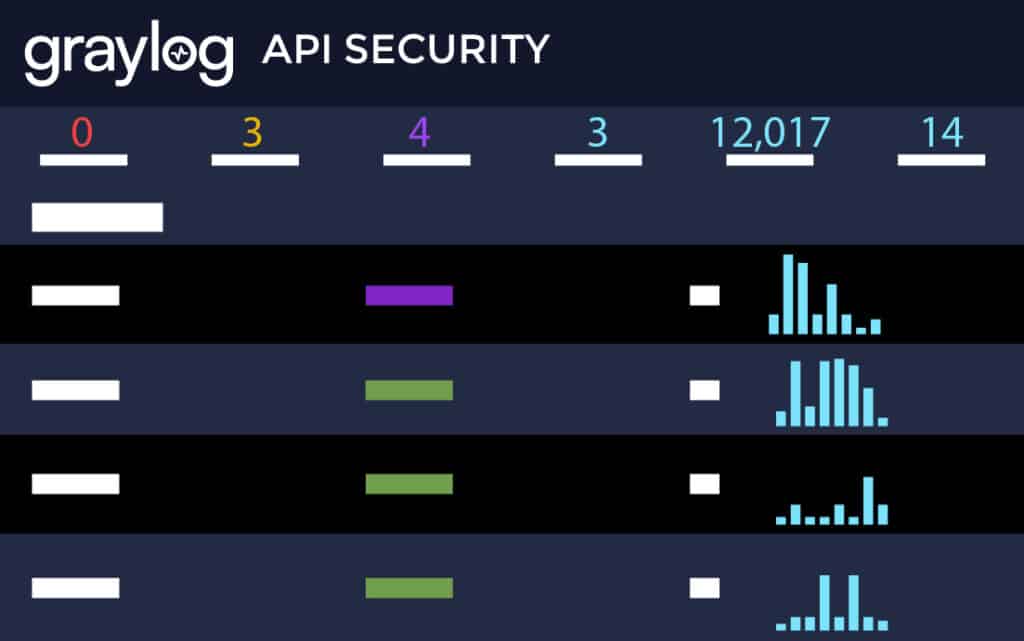
Graylog API Security: Guarding Your Digital Doorways
With the proliferation of web services and cloud-native applications, Application Programming Interfaces (APIs) have become the backbone of digital transformation. However, they also represent potential entry points for attackers. Graylog API security can monitor and protect these interfaces, ensuring that only legitimate requests are processed while detecting and blocking malicious attempts to exploit APIs.
Robust Protection of Digital Assets
Graylog API Security can ensure that your APIs, which often access sensitive data, are safe from exploitation.
Confidence in Meeting Compliance
Many regulations require stringent API security measures. A dedicated solution like Graylog API Security can help you meet these standards, avoiding costly fines.
Graylog Security + Graylog API Security: A Unified Defense Framework
Graylog Security and Graylog API security can provide a multi-layered defense strategy, creating a formidable barrier against cyber threats. While Graylog API security can deliver specialized protection for your APIs, Graylog Security can monitor broader system activities. Together, they provide comprehensive visibility into and control over your entire digital ecosystem.
Holistic Threat Visibility
Gain a 360-degree view of your organization’s security, from general system activities to specialized API transactions.

Enhanced Threat Intelligence
Incorporate threat intel and remediation recommendations from both solutions to derive deeper insights, enabling more accurate threat detection and faster incident response.
Ready to Rise Above the Challenge?
Attackers move fast. Your security teams need to move faster. The evolving threat landscape demands a robust and comprehensive defense strategy. By leveraging the combined strength of Graylog Security and Graylog API Security, you can confidently navigate the cyber realm, ensuring that your assets, reputation, and peace of mind remain intact. Secure your cyber future today with CYBERSECURITY DONE RIGHT.
Resources
Threat Detection & Incident Response (TDIR)
Learn More About Threat Detection and Response
Threat Detection and Incident Response (TDIR) encompasses a range of cyber techniques used to detect, identify, and respond to sophisticated and persistent malware threats. As a Security Informaiton & Event Management (SIEM) solution, Grayl Security is an essential tool organizations can use to analyze log traffic to pinpoint suspicious data, which is a different approach from traditional antivirus software that relies on fingerprint-based detection. Once data is identified as potentilly suspicious, Graylog Security can alert security and IT professionals in real time for analysis.
TDIR is important for maintaining cyber resiliance and is typically part of a layered defense strategy. It helps identify and mitigate threats before they can cause significant damage, strengthening the security posture of an organizatoin.
Advanced Persistent Threats (APTs) are stealthy and prolonged attacks where bad actors establish a foothold in a network to access sensitive data over an extended period. APTs require a sophisticated approach to detection and response, often involving continuous monitoring and analysis to identify and mitigate the attack.
Advanced threat detection works by employing manual or automated methods that isolate suspicious files in a secure environment for analysis, and behavioral analysis of network traffic that compares network behavior against a baseline to identify anomalies. These methods enable the detection of new or dynamic threats that are not recognized by signature-based matching, enhancing the cyber threat detection capabilities of an organization. A threat detection system utilizing advanced threat detection techniques continuously monitors and analyzes data to identify potential threats. By using big data solutions for real-time ingestion and analysis, these systems ensure comprehensive coverage and minimize the chances of overlooking malware, thereby strengthening the IT security incident response framework of an organization.
Other Use Cases
Ready to View Plans?
Get the Monthly Tech Blog Roundup
Subscribe to the latest in log management, security, and all things Graylog blog delivered to your inbox once a month.


