Self-managed log management for teams that want full control without a price tag.
Collect, search, analyze, and act on log data across your entire environment, on your terms. Upgrade when you’re ready.
Graylog Open gives IT operations, DevSecOps, and platform teams the log management foundation they need without vendor lock-in, license walls, or forced infrastructure choices.
Self-host on any infrastructure. Your data, your environment, your rules.
Collect logs from virtually any source and run fast, flexible queries across large datasets.
Connect Graylog to your preferred LLM via free MCP server access. AI-assisted analysis and automation, without a separate add-on.
API-first architecture, plugins, and community content included.
Graylog Open gives IT and DevSecOps teams the visibility and control they need without the cost, complexity, or months of configuration they don’t.
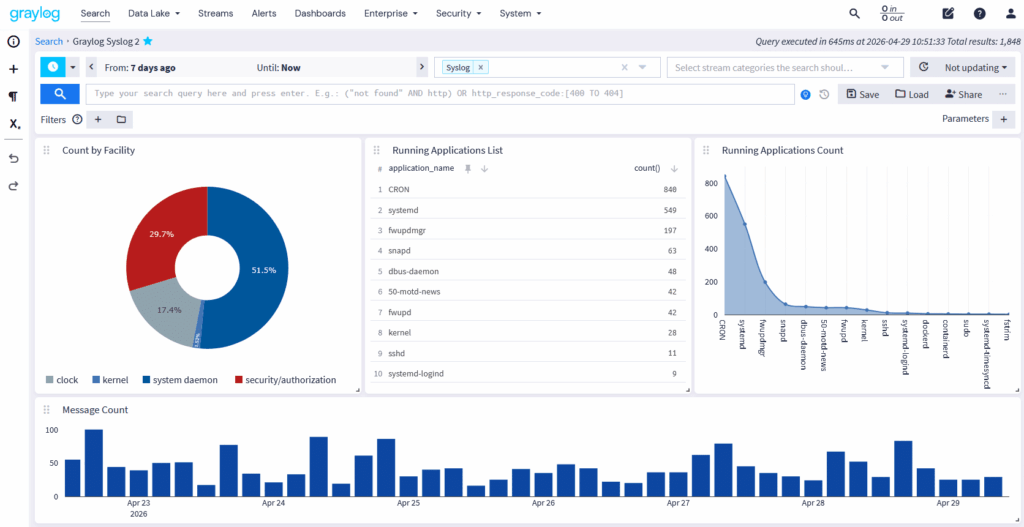
Log data is only useful if you can get to it quickly. Graylog Open ingests from virtually any source (syslog, Windows Events, Kubernetes, cloud services, and more) and makes every message searchable in real time.
Your team shouldn’t spend hours hunting for signals. Graylog Open surfaces them automatically with configurable dashboards, threshold alerts, and event-based notifications, all routable to the tools and channels your team already uses.
Graylog Open is built for teams that want to integrate, automate, and scale without asking permission from a vendor.
Adding nodes shouldn’t mean reconfiguring your entire cluster. Graylog Open handles the operational math so your team focuses on the work, not the maintenance.
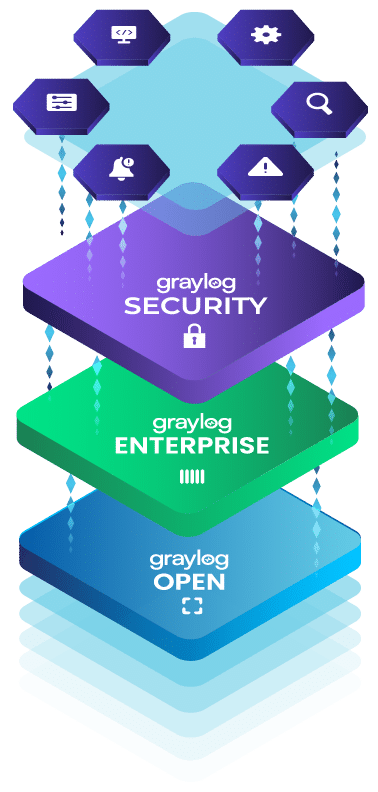
Graylog Open delivers full control over log collection, search, dashboards, and alerting at no cost. When your environment grows, operational demands often grow with it: scaling infrastructure, accelerating incident response, or meeting formal compliance requirements.
Graylog Open is the right fit for teams that can manually investigate alerts, self-manage infrastructure, and operate without formal compliance reporting.
Graylog Enterprise is the right fit when you need to scale log management efficiently:
Graylog Security is the right fit when you need stronger threat detection, incident response, and compliance:
Yes. Graylog Open is free to download and use under the Server Side Public License (SSPL). There are no per-user fees, no ingestion caps, and no time-limited trial. You self-manage the environment, which means you provide the infrastructure and handle your own operations. If your use case involves offering Graylog as a hosted service to others, review the SSPL terms carefully, as specific obligations apply. For teams that need enterprise support, compliance packs, or advanced security capabilities, paid editions are available.
Graylog Open gives you full log collection, search, dashboards, and alerting at no cost. You can ingest logs from syslog, Windows Events, Kubernetes, cloud services, and dozens of other sources. From there, you can build real-time dashboards, create threshold and event-based alerts, run fast guided searches across large datasets, and connect Graylog to your existing toolchain via the REST API. MCP server integration is also included, so you can connect your preferred LLM for AI-assisted log analysis and automation without a paid add-on.
Graylog Open covers the core log management use case: collect, parse, search, alert, and visualize. The paid editions add capabilities that lean and mid-market teams typically need as they grow. Graylog Enterprise adds a built-in data lake, parallel archive restore, dynamic shard sizing, Azure Blob Storage support, value-based licensing, and 24/7 enterprise support. Graylog Security adds SIEM capabilities, including event and asset risk scoring, automated investigation creation, anomaly detection, compliance packs (GDPR, HIPAA), and prebuilt threat detection content. You can compare all three editions in detail on the Compare Plans page.
Yes. Graylog Open runs on Linux, Windows, containers, and cloud infrastructure. You can deploy fully on-premises, fully in the cloud, or across both in a hybrid configuration. There are no restrictions on where you run it. The environment is self-managed, which means your team handles installation, configuration, maintenance, and backups.
Recent releases have added several capabilities that reduce operational overhead and extend what Open teams can do. Dynamic shard sizing now automatically calculates appropriate shard sizes from each node’s available OS memory, removing the need for manual cluster tuning when you add nodes. MCP server integration lets you connect Graylog to your preferred LLM for AI-assisted analysis and automation. You can now import Sigma detection rules directly from private GitHub, GitLab, or Bitbucket repositories. Additional improvements include Quick Jump keyboard navigation, save and load table layouts across sessions, field pinning in message expansion, enhanced PagerDuty notifications with Replay Search links, and a new “Info” event priority tier for lower-noise tracking.
Graylog Open is supported by an active global community through forums, documentation, and user-contributed content. There is no paid SLA-backed support included in the free edition. Teams that need direct access to Graylog’s support engineers, guaranteed response times, or access to Graylog Academy training should consider upgrading to Enterprise or Security, both of which include enterprise support.
Yes. Graylog is designed so that upgrading from Open to a paid edition does not require a platform migration. Your existing log sources, dashboards, searches, and configuration carry forward. The paid editions add capabilities on top of what you have already built, so there is no need to start over. Many teams use Graylog Open to validate the platform and prove value internally before moving to a paid edition.
Most open-source log management tools require significant customization and ongoing maintenance to reach production-ready status. Graylog Open ships with a purpose-built UI, guided search with boolean query support, a REST API, pipeline processing, Sidecar-based agent management, and MCP server integration out of the box. It is also the same core platform that powers Graylog Enterprise and Graylog Security, which means upgrading is additive rather than a replacement. Teams that need log management without a months-long configuration project consistently cite Graylog Open as the fastest path to operational visibility at zero cost.
Start with Graylog Open and upgrade to Enterprise or Security when the time is right.