In today’s intricate IT landscape, organizations face a daunting task: managing and making sense of the vast sea of logs produced by various devices, applications, and systems. These logs, each bearing witness to their originating systems’ events, transactions, and behaviors, are invaluable but can also be overwhelming.

Graylog solutions bring together log data from every part of the IT environment so that it can be organized, enriched, and analyzed. By consolidating logs into a unified platform, you can truly begin to harness your data’s power. Using Graylog, your IT professionals can:
Normalization
Enrichment
Correlation
Fast & Easy Search
Scalability
Archiving
Graylog Enterprise solutions bring together log data from every part of the IT environment so that it can be organized, enriched, and analyzed. By consolidating logs into a unified platform, you can truly begin to harness your data’s power. Using Graylog, your IT professionals can:
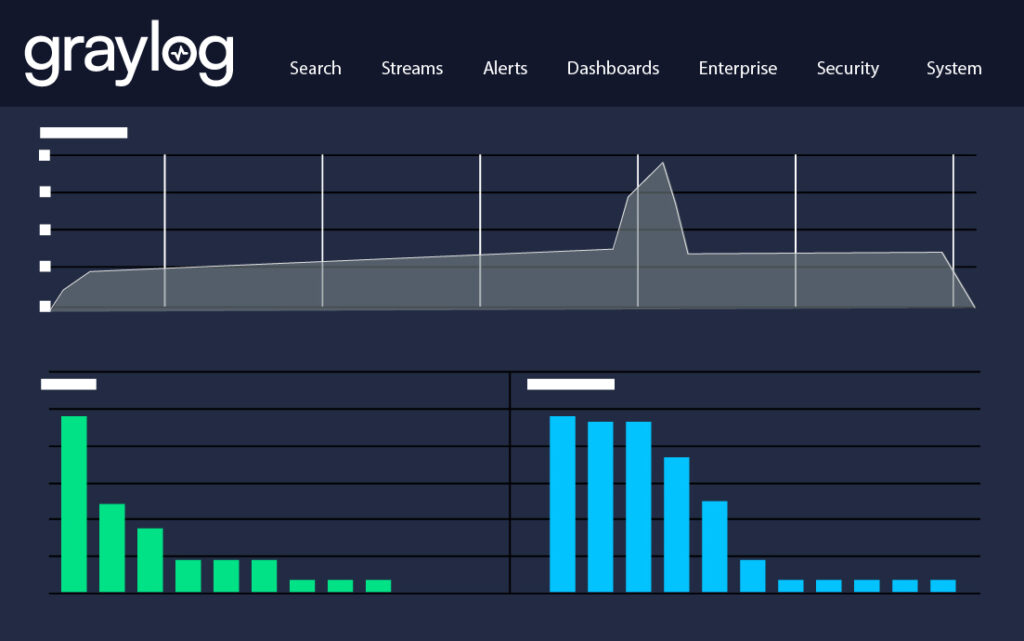
Get a comprehensive, bird’s-eye view of your IT infrastructure: quickly spot patterns, anomalies, and trends across various systems and applications.

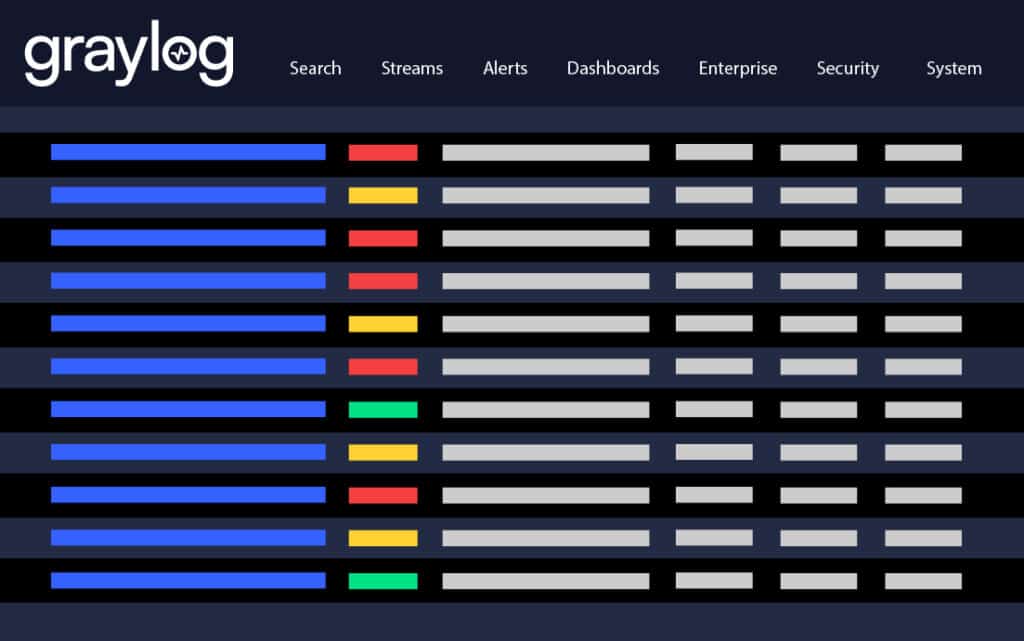
With all your logs in one place, pinpointing issues becomes faster and more precise. Say goodbye to sifting through disparate systems and reduce your mean time to resolution (MTTR).
"Best SIEM and log aggregation tool available right now: The amount of flexibility and insight into logs and operations provided by it are astounding."
- System Administrator in the IT Services Industry
Free up resources and reduce overhead costs associated with managing multiple logging tools. With a centralized approach, your IT team can focus on strategic initiatives and drive innovation.

As owners of the logs, IT Operations teams must also deal with security compliance mandates to collect and retain certain logs and respond to audit requests. Graylog can shrink such tasks from days, even weeks, to minutes.
Navigating the complex maze of log management can be challenging. But with Graylog Enterprise at your side, you can transform this maze into a neatly organized library. Empower your organization to collect and store logs and truly understand and act upon them. Illuminate the depths of your IT operations, simplify compliance efforts, and drive efficiency like never before. Embrace centralized log management and let your data guide you forward.
Centralized Log Management (CLM) is a strategic approach to consolidating all system and application logs in one unified place. Graylog solutions are designed to collect, store, and manage logs efficiently, ensuring every bit of data is within reach when needed and providing a clear, bird’s-eye view of what is happening across your infrastructure and allowing you to answer the daily questions of IT and security operations.
Centralized logging is the process of collecting logs from various sources such as networks, infrastructure, and applications into a single location for storage and analysis, providing a consolidated view of all activity across the network for issue identification and troubleshooting. Decentralized logging, on the other hand, involves managing logs in a dispersed manner, where each source or application handles its own logs independently, often leading to challenges in correlation and connecting the dots for comprehensive analysis.
Centralized logging offers numerous benefits including the ability to store log data from multiple sources in one location, enforce retention policies, search logs easily, generate alerts based on defined metrics, and share information quickly. It significantly reduces the time spent on manual log analysis and improves the efficiency of troubleshooting and monitoring. Additionally, centralized log management systems offer low costs and increased storage for historical data, which is crucial for audits and long-term analysis.
Centralized log management tools offer dynamic scaling to accommodate different types and sizes of infrastructure and handle varying volumes of log data. This scalability ensures that as your business grows, your CLM solution can grow with you, without compromising performance or functionality.
Centralized log management tools handle data retention by providing storage and archiving features that allow organizations to keep their log data for as long as needed. This may include setting retention periods, automating data deletion, and ensuring that data is stored securely and efficiently to optimize storage costs. These options ensure that organizations can comply with regulatory requirements and have access to historical log data for analysis and auditing purposes.
Centralized log management tools support cybersecurity efforts by providing capabilities that enable IT and security teams to monitor, analyze, and respond to security-related events. Features such as data encryption, access controls, and compliance reporting help ensure that sensitive log data is protected and that organizations meet audit and regulatory requirements.
Subscribe to the latest in log management, security, and all things Graylog blog delivered to your inbox once a month.