Centralized log management provides various benefits across an organization. The fundamentals of log management offer a wide variety of business use cases. Whether you’re managing event log data manually or realizing you need more than an Open Source solution, finding the right internal champions can make your life easier. Understanding the business use cases and strategic impact centralized log management provides can help you gain the internal buy-in you need.
Saving time
With all information aggregated in a single location, your teams save time when running queries, enabling development and operations teams to reduce downtime and security teams to reduce mean time to respond.
Development and Operations
Development, Operations, and DevOps teams save time when they’re trying to troubleshoot platform issues. Without centralized log management, your teams fly blind. When an internal or external customer submits a support ticket, Development and Operations teams need to know whether the whole system is down or just part of the system.

To fix these problems, they need to look into the logs. However, in complex IT stacks, the heavy traffic on your applications becomes overwhelming. Tracing errors to the source requires you to look into the logs. Without a centralized log management solution, your teams need to determine what log file it’s in, log into the application, find the right log, and correlate the data. With all the data in one place, you can run queries and filter data to make meaningful correlations that help find the problem faster.
Even more important, if you set alerts for your centralized log management solution, you can locate and fix errors before anyone files a support ticket. By taking a proactive approach, your teams can more effectively and efficiently maintain platform availability.
Security Teams
Security Information and Event Management (SIEM) systems are great at alerting, but they’re not as great at helping security teams locate the threat’s source. They have an analysis tool built in, but they often create problems for threat hunters. Observability tools, also called cardinality tools, aggregate information based on tags, looking for overlaps. This loses the original information.

With centralized log management, every single log stays a single log, so your security teams do the actual forensics incident response and everything else in one place.
Centralized log management gives you the historic information necessary to complete your forensic investigations. Logs act like the digital version of a security camera, tracking how attackers enter systems and where they go once they’re in them. Centralized log management with security analytics tells you someone found an entrance and gives you the evidence necessary to track down how the attacker entered.
Being able to get high fidelity alerts and do your threat hunting in a single location with centralized log management gives your security team the ability to respond to and remediate threats faster.
Saving money
They say that time is money for a reason. Whether you’re trying to keep your platform continuously available to meet SLAs or trying to reduce the time a threat actor is in your systems, centralized log management directly ties to your organization’s financial outcomes.
Development and Operations Teams
Managing log data in the cloud is a way to save money. The pay-as-you-go model means that you can reduce overhead. While this saves money on storage, it costs money if you’re not using a centralized log management solution because your teams can’t effectively and efficiently respond to support tickets. Also, any downtime or extended downtime puts you at risk of violating your Service Level Agreements (SLAs), which can drive customers away.
As the organization scales and adds more users, adding more CPUs and server memory to manage everything costs money. At some point, scaling vertically no longer works because computers have finite memory. The hardware needed to manage the sheer volume of data becomes cost prohibitive.
Now you need to spread out and scale horizontally, so you have multiple machines serving the same application. This leaves your log files on different servers. Spreading the data across different servers saves money from that end only if your teams can quickly respond to support tickets.
Even more difficult for development and operations teams, many companies started putting their log data into containers because they offered the scalability necessary. However, those can be destroyed at any moment. That was the entire design principle underlying them. If the logs are destroyed, your team is flying blind forever because the actual data they need has been deleted with the machine.
The longer they take to find the problem, the longer the platform is going to be down, which can lead to SLA violations. If your platform includes a certain percentage of uptime in the SLAs, you need to detect these problems proactively and resolve them as quickly as possible. Otherwise, your company can lose customers.
Security Teams
According to the 2022 Cost of a Data Breach report, organizations saved $1.12 million dollars by containing a breach in less than 200 days, compared to those who took 200 days or more to contain it. For security teams, time directly relates to money. While using centralized log management may appear obvious for its visibility, it also makes sense for reducing the cost of both data breaches and security monitoring.
Whether you have a dedicated security team or an IT team also tasked with security, centralized log management gives your team the “security camera” they need to detect, identify, remediate, and contain a threat. Centralized log management with security analytics gives you the ability to centralize your data across a decentralized attack surface.
People working from home, whether full- or part-time, isn’t new. It also doesn’t necessarily add new risk, but it definitely amplifies security weaknesses. With people accessing networks from different locations and their own workstations, your security team needs greater visibility into what workstation or user account is the attack vector. Since centralized log management aggregates all that data into one location, you can make the most of all your security tools.
Example
If a new wave of ransomware starts with a warming behavior by jumping from host to host to host to host, you need to know which employee is the attack vector. When your centralized log management solution includes UEBA with machine learning (ML), you can create high fidelity alerts that incorporate user identity, device, and abnormal access then search for the checksum to locate what people downloaded. By doing this in a single location, your security team can investigate faster and collect the necessary forensics on the machines even if you can’t physically get to them.
Streamlining compliance
Whether you need to comply with regulations, industry standards, SLAs, or internal controls, centralized log management streamlines the process.
Development and Operations Teams
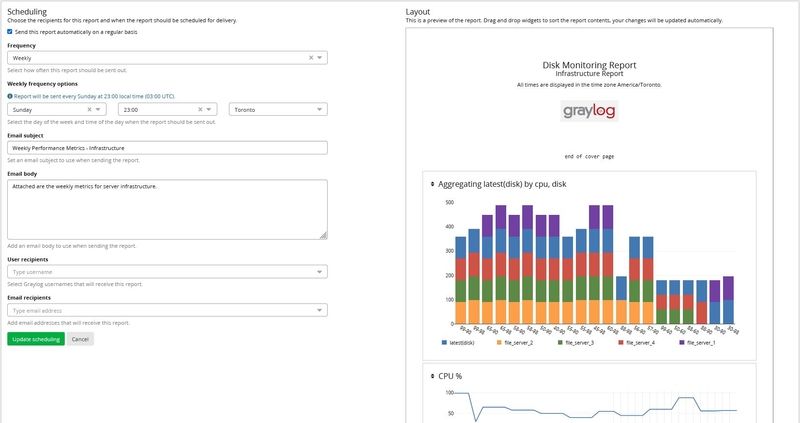
Having all your logs in a single location is one thing. Getting them organized so that you can provide easy to understand reports is another. Centralized log management gives you the dashboards and reporting capabilities you need to prove your compliance with internal controls and SLAs.
Example
To prove that they’re following best practices, your development team needs to show that they tested the application before deploying it. As part of this, they can use logs to show that no errors were detected and that the software worked as intended before they pushed the application to production.
Security Teams
Whether a security incident occurs or not, your security teams face increasing scrutiny. New laws, industry standards, and contracts incorporate security audits. The sheer volume of information is difficult to pull together as part of your audit. With centralized log management, your security teams can create dashboards and reports that respond to your audit requirements. Instead of working overtime to respond to a document request, they can set the report requirements and run the report when asked.
Graylog Security and Operations Analytics
Building a business use case for centralized log management is often easier than people think it will be. Whether you’re talking about your internal or external customers, centralized log management provides a better end-user experience. They will experience fewer errors, and get a more stable, more secure platform.
Graylog Security gives your IT and security teams the analytics they need for collaboration, cost-savings, and reporting. With our lightning fast speed, your teams can investigate incidents – security or otherwise – more rapidly, ensuring less downtime and enhanced monitoring.