In a world where attackers can move fast, security teams need to move faster. According to SANS research from 2022, adversaries can perform intrusion actions within a five-hour window. While analysts need the Millennium Falcon of security technologies that enable threat detection and response in under twelve parsecs, increasingly complex IT environments make the 1-10-60 Framework feel unachievable. Overwhelmed with false positives, security analysts struggle to efficiently detect risky behavior, investigate incidents, and remediate their environments.
To build cyber resilient programs, security teams need technologies that enable rapid threat detection and response.
What is threat detection and response?
Threat detection and response (TDR) is the set of processes and the supporting technologies that enable security teams to identify network, application, and digital asset threats as quickly and accurately as possible. Typically, TDR includes:
- Security monitoring
- Anomaly detection
- Alert validation
- Threat analysis and prioritization
- Incident investigation
- Incident response and recovery
With TDR, security teams correlate threat indicators, analyze user behaviors, and monitor activities occurring in their environments to identify:
- Known threats using signatures
- Unknown threats with user and entity behavior analytics (UEBA)
- Evasive malware attacks, including zero-day exploits and advanced persistent threats (APTs)
What is the difference between threat detection and threat hunting?
While threat detection and threat hunting may overlap, threat detection is a broader category of activities that security teams undertake before, during, and after an incident occurs. Meanwhile, threat hunting is a proactive process where security analysts use their security tools to identify threat activity before malicious actors steal data. Threat hunting typically includes:
- Leveraging threat intelligence to look for behavioral patterns before a detection alert fires
- Testing hypotheses and following clues to look for adversaries hiding in systems
- Continuously treating systems, networks, devices, and users as though they have already been compromised
What are the benefits of threat detection and response?
Threat detection and response enables you to mitigate data breach risks and build a cyber resilient program.
Rapid detection
The faster you can detect a threat, the faster you can mitigate damage. Your threat detection alerts become the first step in the response process. With high-fidelity alerts, you can respond faster, ultimately mitigating a threat’s impact to your data and business.
Faster investigation
With the high-fidelity alerts, you know that what you’re investigating is really an important incident. Since you’re not spending time chasing down false alerts, your investigations become more meaningful by focusing on real data threats.
Reduced dwell time
With threat detection and response capabilities, you can detect and prevent advanced threats. The less time threat actors spend, or dwell, in your systems, the less damage they can do. When your security monitoring enables you to identify known and unknown threats, you can contain attackers, even if they manage to bypass traditional defenses.
Increased visibility
The technologies that enable threat detection and response centralize security event monitoring and event correlation across a company’s IT environment. Since you’re looking at more data, you have greater visibility into interconnected applications, networks, and devices.
5 Best Practices for Implementing Threat Detection and Response with Centralized Log Management
A centralized log management solution with security analytics gives you threat detection and response capabilities.
Consolidate all logs in a single location
No matter what technology you choose, your first step to robust threat detection and response is collecting and aggregating all log data in a single location where you can correlate and analyze events. In modernized IT environments, you need visibility across:
- User access
- Endpoint security
- Network activity
- Application security
When aggregating your log data, you gain visibility across multiple security dimensions and your environment.
Leverage threat intelligence
Threat intelligence enables you to understand the security risks that your organization faces by incorporating situational awareness around:
- Geographic location
- Industry vertical
- Operating system and software vulnerabilities

With situational awareness, you can prioritize alerts to investigate, contain, remediate, and recover faster.
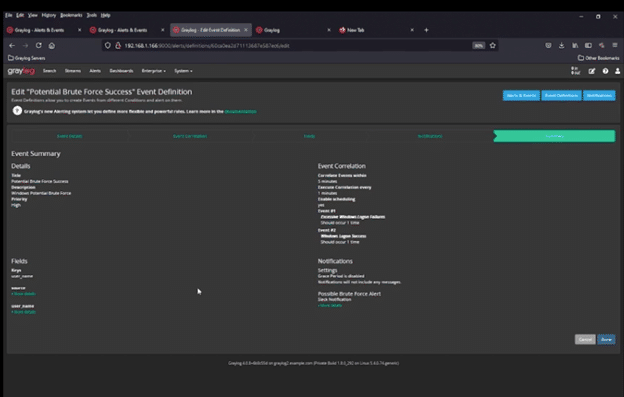
Build high-fidelity alerts
If your technology aggregates log data and threat intelligence, you can build high-fidelity alerts for enhanced detection. When you can correlate multiple events and supplement that with threat intelligence, you have a lower false-positive rate, meaning that you know alerts are important.
Automate processes
Data analytics is critical to automating threat detection and response. For real-time monitoring and response capabilities, machine learning (ML) with data analytics gives you the ability to respond to the continuously evolving threat landscape in a dynamic ecosystem. For example, anomaly detection leveraging UEBA enables you to identify changes to user and entity behaviors while continuously fine-tuning itself for improvement over time.
Additionally, you can create correlated searches and dashboard that mature your cybersecurity threat detection and response. Rather than manually searching the same information every day, you can design dashboards in your centralized log management solution that automatically give you the data you need, when you need it.
Engage in threat hunting
To level up your threat detection and response capabilities, you should proactively look for hidden threats. As a subset of threat detection, threat hunting enables you to create a comprehensive approach that focuses on known and unknown threats. Sophisticated threat actors can gain access to and hide in systems and networks.
While reactive threat detections enable you to investigate active incidents more rapidly, threat hunting enables you to prevent an incident from becoming active.
Graylog Security: The Right-Sized Threat Detection and Response Solution
Using Graylog Security, you can achieve your threat detection and response program goals by focusing on the functionality you need without the complexity and cost of a traditional Security Information and Event Management (SIEM) technology. By leveraging our cloud-native capabilities and out-of-the-box content, you gain immediate value from your logs. Our anomaly detection ML improves over time without manual tuning, adapting rapidly to new data sets, organizational priorities, and custom use cases so that you can automate key user and entity access monitoring.
With our intuitive user interface, you can rapidly investigate alerts. Our lightning-fast search capabilities enable you to search terabytes of data in milliseconds so that you can reduce dwell times, shrinking investigations by hours, days, and weeks.
To learn how Graylog Security can help you implement robust threat detection and response, contact us today.


