It’s been a really long few years in IT. You’ve been working nearly ‘round the clock. First, it was “get everyone remote and productive!” Then it was, “make sure everything is secured!” Now, it’s “we need to document everything with all the new security and privacy compliance requirements!” It’s easy to feel like you’re stuck in a perpetual hamster wheel, running continuously and going nowhere.
Using centralized log management for security and compliance releases that hamster wheel so you can start moving forward and prove that your work has made a difference.
WHAT IS LOG MANAGEMENT AND ANALYSIS?
Every user, device, operating system, software, and network generates event log data, pieces of information detailing all actions across your systems. Traditionally, IT departments use event log files to:
- Optimize performance
- Identify technical issues
- Manage resources
- Monitor security controls
- Document compliance
Typically, each log contains the following data:
- Date stamp
- Timestamp
- Username
- Machine/Computer
- Event ID
- Source (application or component)
- Type of event
Log management is the systematic process of collecting and analyzing event and security logs to understand everything happening within your environment.
WHAT IS CENTRALIZED LOG MANAGEMENT?
At its most basic level, centralized log management makes it easier to search through data to get the insights you need in a way that you can use. Complex environments across on-premises, hybrid, and multi-cloud deployments can generate terabytes of log data every day. If you don’t have all this information in a single location, you won’t be able to find what you’re looking for when a security incident occurs.
Centralized log management formalizes these processes by:
- Aggregating all logs in a single location
- Parsing the data to extract only what you need
- Normalizing the data, so everything is in the same format
- Correlating the data to discover interrelated activities in complex environments
USING CENTRALIZED LOG MANAGEMENT FOR SECURITY
Since event and security logs tell you what’s happening in your environment, they give you details that support key security functions like:
- Access monitoring
- Network monitoring
- Endpoint security
- Patch management
- Data exfiltration/data loss
- Incident and response
With the right centralized log management solution, you have the ability to:
- Automate threat hunting
- Create high-fidelity alerts
- Remediate vulnerabilities
- Investigate incidents
USING CENTRALIZED LOG MANAGEMENT FOR COMPLIANCE
Over the last few years, governments and industry standards organizations have added more compliance requirements. While compliance is not security, it is important to your senior leadership because they don’t want to pay fines or lose customers.
Centralized log management gives you the documentation you need, proving your cyber resilience and reducing the time that audits take.
With the right centralized log management solution, you can:
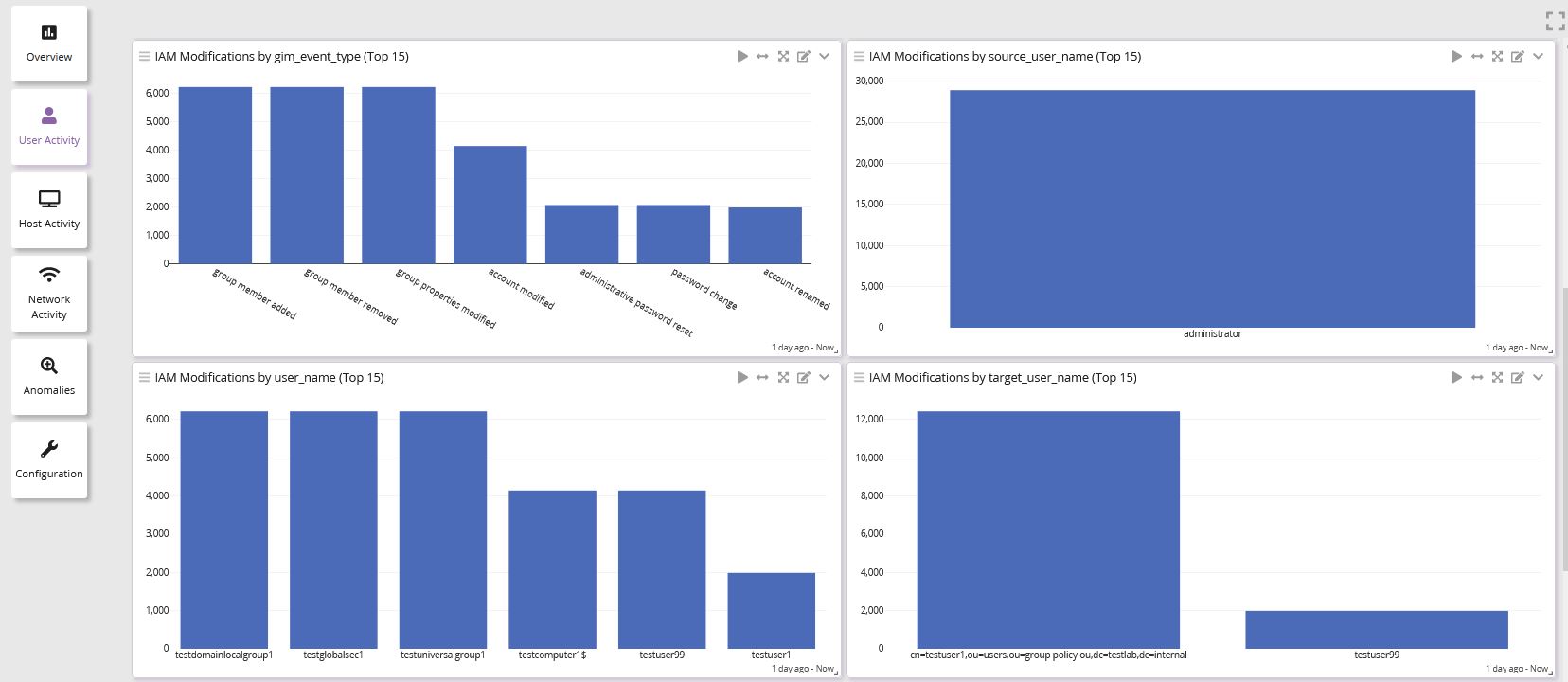
- Create dashboards that use visualizations for easy-to-understand insights
- Show trends over time that support your security posture
- Forward dashboards to internal stakeholders, including IT, security, and senior leadership teams
- Schedule reporting to meet compliance mandates timelines
WHAT IS THE DIFFERENCE BETWEEN CENTRALIZED LOG MANAGEMENT AND A SECURITY INFORMATION AND EVENT MANAGEMENT SYSTEM(SIEM)?
Depending on what you need and the centralized log management solution, there might not be a lot of differences between the two.
You could argue that SIEMs started as security tools while centralized log management started as an IT operations tool. However, digital transformation has changed centralized log management just as it has evolved other business-critical technologies.
According to Gartner, a SIEM usually has capabilities for:
- Threat detection
- Compliance
- Collection and analysis of security events
- Event and contextual data sources
- Log event collection and management
- Log event analysis that incorporates additional data
- Operational capabilities like incident management, dashboards, and reporting
Most modern centralized log management solutions incorporate security analytics that correlates threat intelligence with data analytics making them an effective cybersecurity software platform. For example, a centralized log management solution that can provide similar capabilities to a SIEM includes:
- Pre-build security scenarios that address common use cases
- Risk models that adapt to the organization’s priorities
- Robust alerting to detect common threats
- Log data enrichment with threat intelligence for context
HOW DO YOU IMPLEMENT CENTRALIZED LOGGING FOR SECURITY AND COMPLIANCE?
Most IT operations teams already have a centralized log management tool. If yours has the analytics and data enrichment needed, you should be able to use it as a security analytics tool.
CREATE A STRATEGY
If you’re starting your centralized log management implementation from scratch, the first step is knowing what information you need to collect.
For security and compliance, you should consider logs from:
- Identity and Access Management (IAM) tools
- Firewalls
- Endpoint Detection and Repsonse (EDR)
- Patch management tools
- Network devices (routers, switches)
- Servers/Hosts
IDENTIFY SECURITY USE CASES
When using centralized log management for security analytics, you need to plan out your use cases as part of your strategy.
Some typical use cases include:
- Security hygiene
- Detection
- Threat hunting/investigation
- Forensics
- Secure Software Development Life cycle (SSDLC)
CREATE DASHBOARDS FOR COMPLIANCE
Centralized log management gives you dashboards that your senior leadership can use to meet their governance compliance requirements.
When you create these dashboards, you want to consider some of the following compliance reporting needs:
- Assessing risk
- Continuous monitoring
- Incident response
- Reporting to the Board of Directors
Once you create the dashboards, you can change the date parameters to provide internal and external auditor’s reports. Instead of spending days responding to an audit documentation request, you can spend a few hours providing all the information your auditor needs.
GRAYLOG: CENTRALIZED LOG MANAGEMENT FOR SECURITY AND COMPLIANCE
Graylog Security is designed to give you the analytics you need with the user experience you want at a price you can afford. With our high-fidelity alerts, you get faster detection times that help you level up your security posture. Our lightning-fast speed and easy-to-use search parameters mean that your team can work more efficiently to achieve faster mean time to investigate (MTTI) and mean time to remediate (MTTR) without needing the specialized skills that many SIEMs require.