As governments continue to digitize services, the number of systems that support public administration continues to grow. With this expansion comes greater cybersecurity risk. To address these risks, Spain established the Esquema Nacional de Seguridad (ENS), a national framework designed to protect information systems used by public sector organizations.
ENS defines the security requirements that ensure government systems remain secure, reliable, and resilient. These requirements apply not only to government institutions but also to private organizations that provide technology or services to the Spanish public sector.
Organizations that fall within the framework must implement controls for monitoring, incident response, and security oversight. One of the most important capabilities supporting these requirements is centralized log management with security analytics.
What is the ENS Framework?
The Esquema Nacional de Seguridad (ENS) is Spain’s national cybersecurity framework that defines the security controls required to protect information systems used by public administration and organizations that support government services.
It defines the security principles, controls, and monitoring requirements that organizations must implement to protect government data and digital services.
ENS was first introduced in 2010 and later updated through Royal Decree 311/2022, which strengthened the framework to address modern cyber threats and digital infrastructure.
The framework focuses on protecting five key security principles:
- Confidentiality – ensuring sensitive information is only accessible to authorized users
- Integrity – preventing unauthorized modification of data
- Availability – ensuring systems and services remain operational
- Authenticity – verifying the identity of users and systems
- Traceability – maintaining records of system activity for auditing and investigation
These principles guide the security controls organizations must implement when operating or supporting public sector systems.
Who Must Comply with ENS?
ENS applies primarily to Spanish public administration organizations, but its reach extends beyond government agencies.
Organizations that may fall within ENS requirements include:
- National, regional, and municipal government entities
- Public administration departments
- Technology vendors serving government institutions
- Managed service providers
- Cloud service providers supporting government workloads
- Software vendors selling solutions to public sector organizations
In many cases, companies must demonstrate ENS compliance or certification before they can provide technology or services to the Spanish government.
For technology providers operating in Spain, ENS compliance is often a prerequisite for participating in public sector contracts.
ENS Security Categories
ENS classifies systems into three security categories based on the potential impact of a security incident.
Basic Category
Systems where an incident would have minimal operational impact.
Medium Category
Systems where a disruption could affect government services or operational processes.
High Category
Systems where a compromise could severely affect public services, sensitive data, or national interests.
The assigned category determines the number and rigor of security controls required.
Higher-impact systems must implement stronger monitoring, incident response, and security oversight capabilities.
Key ENS Security Requirements
ENS defines a set of organizational, operational, and technical measures designed to create a consistent security baseline across government infrastructure.
Key areas include:
- Risk management and governance
- Identity and access control
- System monitoring and logging
- Incident response capabilities
- Business continuity and disaster recovery
- Network and infrastructure protection
- Vulnerability management
- Asset inventory and system configuration control
Organizations must also maintain documentation demonstrating that these controls are implemented and functioning properly.
Regular audits may be required to verify compliance.
Monitoring and Traceability Requirements
One of the core ENS principles is traceability.
Traceability requires organizations to maintain detailed records of system activity so security teams can investigate incidents and reconstruct events.
To meet this requirement, organizations must collect and retain logs from systems such as:
- Servers and operating systems
- Network infrastructure
- Security appliances
- Identity management systems
- Applications and databases
These logs must be stored securely and made accessible for investigation and auditing.
Without centralized logging and monitoring capabilities, meeting ENS traceability requirements becomes significantly more difficult.
Centralized Log Management for ENS Compliance
Centralized log management plays a critical role in meeting ENS monitoring and investigation requirements.
By aggregating log data from across the environment, organizations gain visibility into system activity and potential security events.
A centralized logging platform allows security teams to analyze activity across:
- Users and authentication systems
- Network infrastructure
- Endpoints and servers
- Applications and services
- Security tools and detection systems
Platforms that combine logging with security analytics and SIEM capabilities allow teams to correlate activity across systems and detect suspicious behavior earlier.
Centralized log management also improves response time by enabling security teams to search and analyze data from multiple systems in one place.
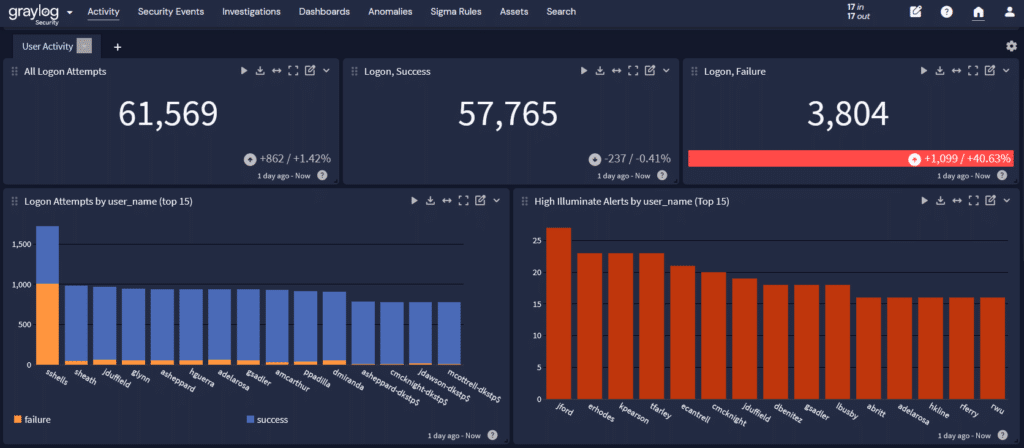
Access Monitoring
Identity-based attacks remain one of the most common methods used by threat actors. Monitoring authentication and access events is critical for detecting suspicious activity.
With security analytics, authentication data can be analyzed to identify patterns such as:
- Repeated login failures
- Privileged access misuse
- Suspicious account activity
- Unauthorized privilege escalation
- Logins from unusual locations or times
These capabilities support ENS requirements related to identity management and access control.
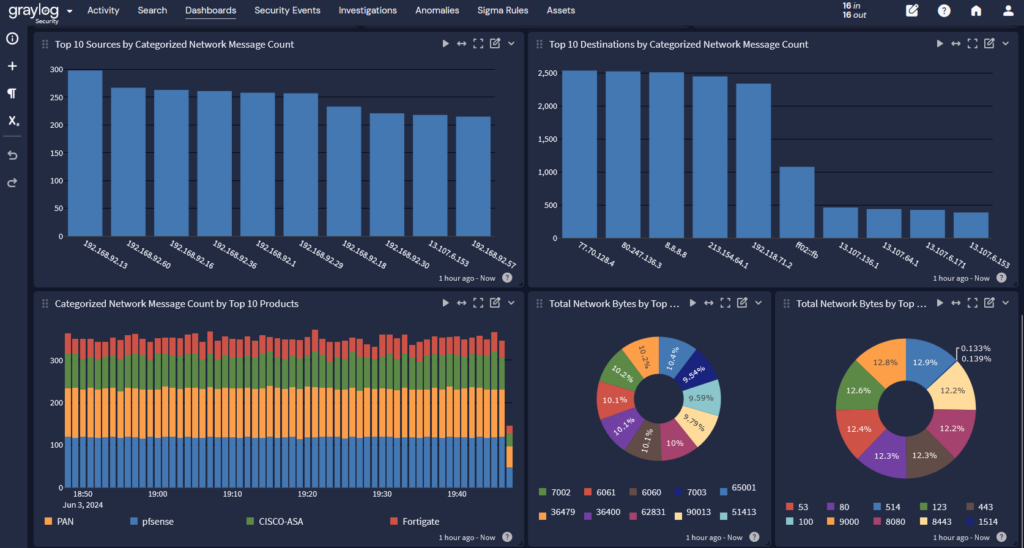
Network Monitoring
Network monitoring helps detect suspicious activity that could indicate unauthorized access or attempted system compromise.
Logs from firewalls, network appliances, and security tools provide important insight into network behavior.
Monitoring these logs allows organizations to detect:
- Unusual traffic patterns
- Communication with suspicious external hosts
- Lateral movement inside the network
- Intrusion attempts
When combined with security analytics, these data sources help identify anomalies that may signal a developing security incident.
Monitoring for Data Exfiltration
Threat actors often attempt to extract sensitive data once they gain access to a system.
Detecting unusual data movement is critical for preventing information loss.
Security monitoring tools can detect potential data exfiltration by analyzing:
- Large file transfers
- Unusual download patterns
- Access to sensitive datasets
- Transfers to unknown external destinations
Correlating logs from endpoints, network tools, and applications improves visibility into potential data theft attempts.
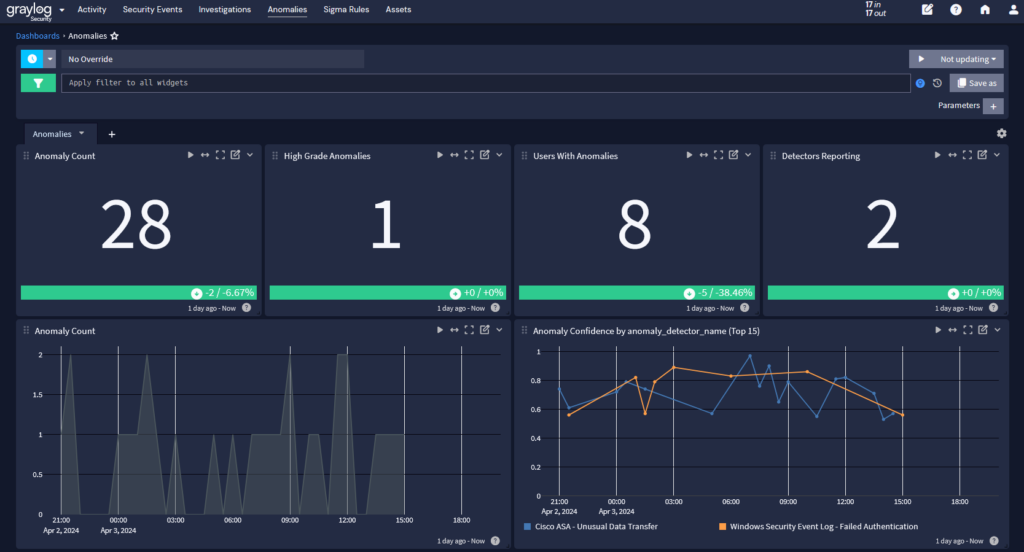
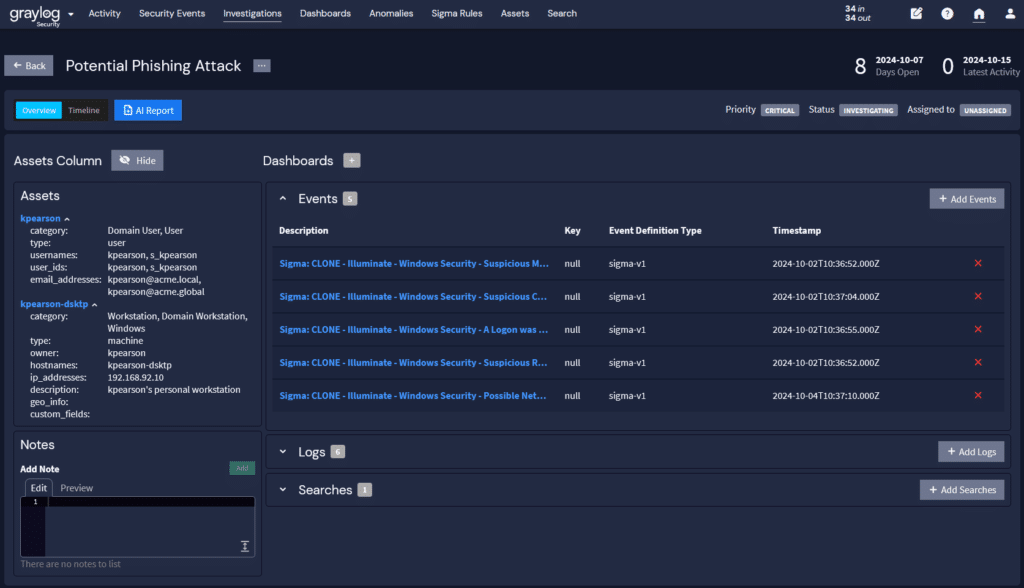
Incident Investigation and Threat Detection
ENS requires organizations to maintain the ability to investigate incidents and determine what occurred within affected systems.
Security teams must be able to quickly analyze logs to identify the timeline of an attack and determine how the incident developed.
Rapid analysis requires high-speed search and investigation capabilities that allow analysts to reconstruct events across large volumes of log data.
Threat detection tools allow analysts to search for indicators such as:
- Abnormal user activity
- Suspicious system resource usage
- Unusual file access behavior
- Unexpected configuration changes
- Sudden spikes in network traffic
Rapid search capabilities enable security teams to respond faster and reduce the impact of incidents.
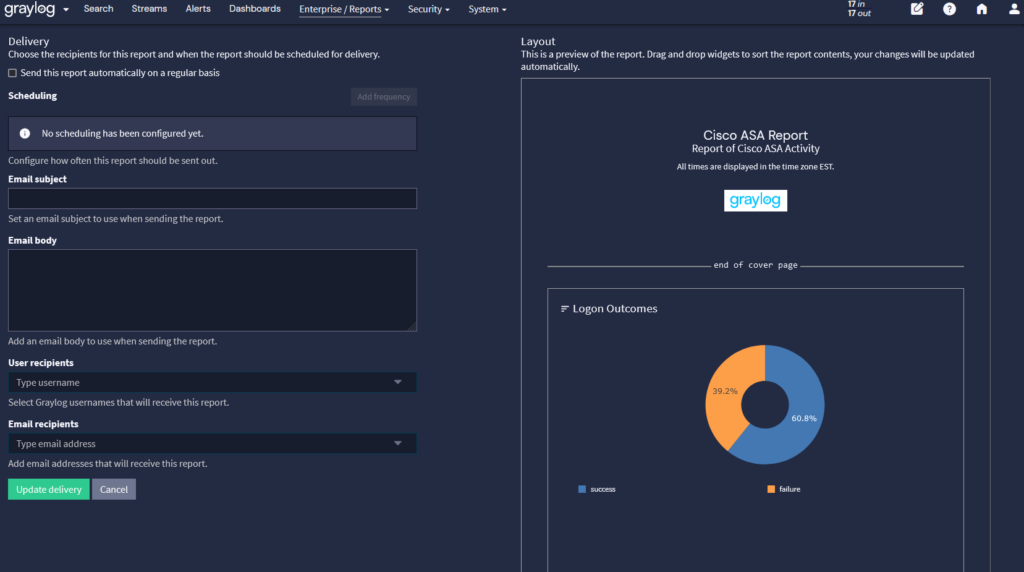
Compliance Reporting and Security Oversight
Organizations operating under ENS must maintain documentation demonstrating their security posture.
Security dashboards and reporting tools help teams produce the information required for internal review and regulatory audits.
These tools support compliance monitoring by helping organizations document:
- Incident timelines
- Root cause analysis
- Security control implementation
- System activity logs
- Response and remediation actions
Having centralized monitoring and reporting tools simplifies the process of collecting and presenting this information.
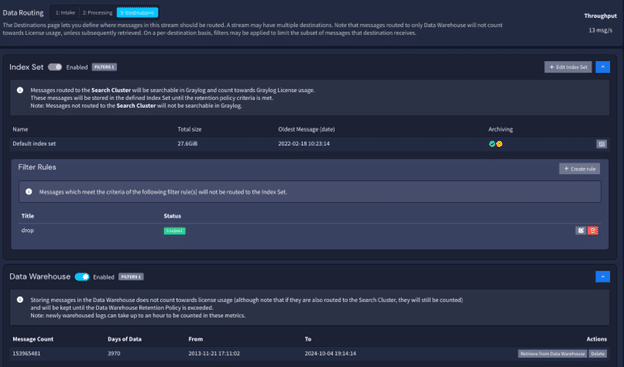
Data Governance and Control
ENS places strong emphasis on traceability and accountability, requiring organizations to retain system activity records so incidents can be investigated and audited when necessary.
A centralized logging platform helps organizations meet these requirements by providing control over how log data is collected, stored, and accessed across the environment.
Graylog supports strong data governance capabilities, including:
- Long-term log retention to ensure historical security data remains available for investigations and compliance audits
- Data tiering, allowing frequently accessed data to remain in high-performance storage while older data moves to more cost-efficient storage tiers
- Data routing, enabling organizations to direct specific log streams to different destinations, such as a data lake for long-term analysis and archival
Graylog also provides deployment flexibility, allowing organizations to run the platform:
- On-premise within their own infrastructure
- In public or private cloud environments
- In hybrid architectures combining on-premise systems and cloud storage
This flexibility helps organizations maintain control over where sensitive data resides while still supporting scalable log management and ENS compliance requirements.
Risks of Non-Compliance
Failure to comply with ENS can create operational and business risks for organizations that support the Spanish public sector.
Consequences may include:
- Loss of eligibility for government contracts
- Mandatory remediation requirements
- Increased regulatory oversight
- Operational disruptions
- Reputational damage
For organizations that depend on public sector partnerships, ENS compliance is often necessary to maintain business relationships.
How Graylog Helps Support ENS Monitoring and Data Governance Requirements
Meeting ENS monitoring, traceability, and investigation requirements depends on strong visibility and control over system activity data.
Graylog provides centralized log management and security analytics capabilities that help organizations monitor infrastructure activity, investigate incidents, and maintain the data governance controls required for ENS compliance.
With Graylog, organizations can:
- Collect and centralize logs from across their infrastructure
- Correlate security events from multiple systems to identify suspicious activity
- Detect threats using alerts and anomaly detection
- Investigate incidents using high-speed search across large volumes of log data
- Maintain long-term log retention to support audits and incident investigations
- Optimize storage using data tiering, keeping recent data in high-performance storage while moving older data to lower-cost tiers
- Route specific log streams to external systems or data lakes for long-term archival and analysis
- Deploy Graylog on-premise, in the cloud, or in hybrid environments, allowing organizations to maintain full control over where their data resides
These capabilities help security teams maintain the visibility, traceability, and data governance controls required to support ENS compliance.
To learn more about how Graylog can support your ENS monitoring and compliance strategy, contact our team.