At a high level, incident remediation is a part of the incident response process. An Incident response plan manages the incident lifecycle across planning, detection, investigation, and recovery. Meanwhile, incident remediation focuses on identifying root causes and implementing measures to prevent future occurrences.
While planning a response and detecting an incident is difficult, many security teams struggle with incident remediation, especially when faced with smaller teams or less experienced analysts. With insight into the differences between incident response and incident remediation, security teams can create more effective and efficient processes for handling future attacks.
What Is Incident Remediation?
Incident remediation addresses and eliminates an incident’s root cause and its effects. While incident response deals with immediate containment and resolution, remediation implements long-term solutions that mitigate future incidents.
Incident remediation typically manages:
- Root Cause Analysis: Identifying and addressing an incident’s underlying cause.
- Residual Effects: Resolving any lingering impacts of the incident.
- Learning and Improving: Using insights gained from the incident to strengthen defenses.
- Proactive Measures: Addressing weaknesses across people, processes, and technology to mitigate future risk.
Incident remediation takes an informed and strategic approach to restoring normal operations and preventing future security breaches. It goes beyond reacting to incidents to include proactive measures to enhance the organization’s security posture.
What Are The Key Differences Between Incident Response and Incident Remediation?
To understand how incident response and incident remediation support each other, you need to define their differences clearly.
What: The Primary Objective
An effective incident response program focuses on the actions that detect, analyze, contain, and communicate a cybersecurity incident while in the heat of the moment. Meanwhile, incident remediation focuses on the long-term actions that eliminate the incident’s root cause and prevent another incident arising from the same issues.
More succinctly, the two have different primary goals:
- Incident response: Minimize damage and restore normal operations quickly.
- Incident remediation: Fix vulnerabilities, improve defenses, and prevent a repeat of the same issue.
When: Timing of Activities
You can think of the timing like a Venn diagram. Some of the activities happen simultaneously, but the majority occur at different times:
- Incident response: During or immediately after the incident occurs.
- Incident remediation: After managing initial response activities, once the situation is under control.
How: The Key Activities
Similar to the timing differences, the key activities for each process may overlap somewhat, but they have very distinct differences.
Incident response activities typically include:
- Incident identification and alerting
- Triage and initial investigation
- Containment and mitigation
- Communication with senior management and other stakeholders
Meanwhile, incident remediation activities typically include:
- Root cause analysis
- Patching systems
- Updating firewall rules or security policies
- Improving monitoring or training
The two processes are not entirely distinct from each other. For example, the initial investigation supports the root cause analysis by giving security teams insight into the impacted systems and networks. Additionally, terminating access to an impacted account or network segment is part of containment but may also involve updating firewall rules or security policies.
Who: The Responsible Parties
As the activities overlap and diverge, the people involved are similar and different:
- Incident response: Security operations center (SOC) or security incident response team.
- Incident remediation: IT operations, security architects, and system owners, often collaborating with the incident response stakeholders.
Why: The Documentation
From communications to compliance, you need to document both processes, but the information will be different:
- Incident response: Real-time documentation of what happened and the activities taken to manage it.
- Incident remediation: IT security incident reports detailing the fixes you applied and the policies or procedures you need to revise.
What Are The Challenges Security Teams Face During Incident Remediation?
For many security teams, incident response and incident remediation seem like the same thing, especially when thinking about the containment and eradication processes. However, since the response and remediation have different objectives, you should understand challenges specific to incident remediation.
Root Cause Identification
While the containment and eradication processes require incident investigations, identifying the incident’s actual root cause is challenging in complex IT environments. Some examples of root causes could include:
- Misconfigurations
- Unpatched vulnerabilities
- Malicious or accidental insider threats
While incident response focuses on symptoms and potential impact, incident remediation requires deep technical investigations and forensic analyses.
Legacy Systems and Technical Debt
While the incident response process may require you to isolate a system, the incident remediation process may require you to update old systems or replace legacy technologies.
For example, many organizations maintain devices that rely on operating systems that manufacturers no longer support, meaning the technologies have no security updates to close vulnerabilities. The remediation process requires you to replace these technologies or implement compensating controls that mitigate the security risk.
Cross-Team Collaboration
Remediation is more than a security function. Often, the activities that prevent attackers from deploying the same or similar attacks require you to collaborate across IT, DevOps, security, and lines of business. Everyone involved needs access to the same information so that you can collaborate effectively.
Change Management
Maintaining business operations is key to having an incident response process that promotes resilience. However, the changes that remediation requires often include activities that disrupt service availability or introduce new issues, including:
- Applying patches.
- Updating configurations.
- Updating software to newer versions.
Policy and Process Gaps
Remediation often requires you to identify gaps in policies or controls that allowed the incident to occur. While incident response focuses on tactical activities, incident remediation requires strategic, long-term improvements that are more difficult to enforce and measure.
Validation of Fixes
While response seeks to stabilize environments quickly, remediation activities require testing and validation to ensure the fixes work as intended. Plus, you must ensure these fixes do not introduce new vulnerabilities.
Compliance Documentation
After a security incident, you must prove that your controls worked as intended to reduce the risk of fines and penalties arising from compliance violations. However, your fixes need to meet, at least, the same level of scrutiny. You need to document any remediation activities and provide the appropriate audit trails, reporting, and compliance validations for them.
3 Ways to Improve Incident Remediation Processes
Since incident response and incident remediation seem similar on the surface, many organizations treat them as the same thing. However, security teams should consider how they can improve their incident remediation processes as part of upleveling their overall security program.
Centralize All Security Activities
When you use a centralized platform for managing all security activities, you can organize and track investigation in a single location. By aggregating all this data, you can store alerts, logs, queries, dashboards, and findings in one place so that everyone who needs access to them has the appropriate level of access. For example, while a security team needs write/edit access to the incident information, the DevOps team may only require read access. By consolidating the data and limiting access according to job function, you enhance collaboration.
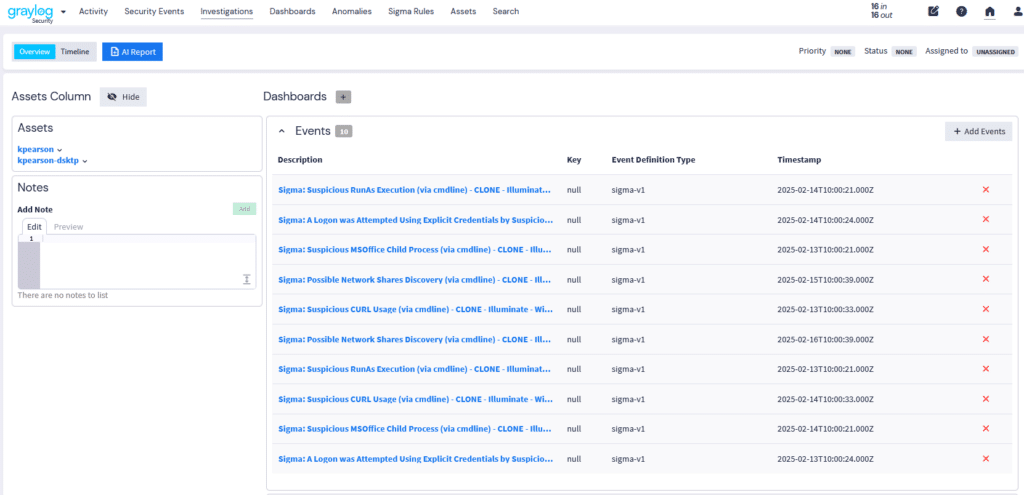
Create Timelines
Your detections and alerts start the incident response process. However, as part of the root cause investigation, you need to know all the different individual events that occurred and when they occurred. By creating an event timeline within your centralized security platform, you gain visibility into how attackers gained initial access and how they moved across the environment. With these insights, you can look at the different systems, networks, applications, devices, and user accounts impacted to help identify potential areas of remediation.
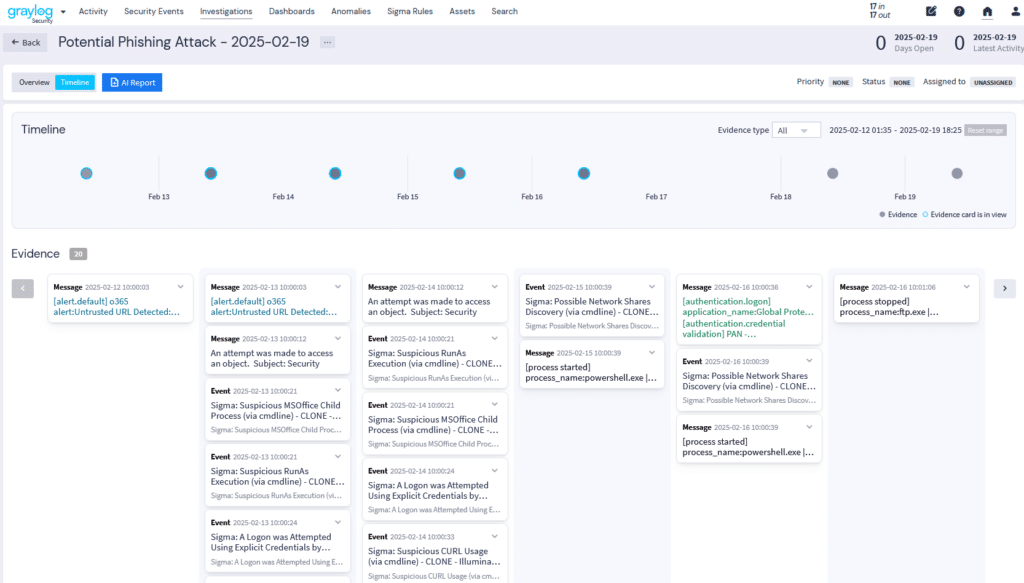
Leverage Artificial Intelligence (AI)
Preparing the post-incident security reports is a critical part of the incident remediation process. Since generative AI can take in large amounts of data and summarize it well, you can use it to extract important details and summarize the data that the incident generated.
With generative AI models, you rapidly build reports that include:
- Event and evidence summaries
- Event analyses
- Explanation of root cause
- Suggestions for containing and eradicating threats

Graylog Security: Enhanced Incident Remediation to Improve Overall Security Posture
With Graylog Security investigations management capabilities, you can more rapidly investigate incidents and document activities to streamline the incident remediation process. Graylog Investigations centralizes logs, evidence, and collaboration tools so that you can move smoothly from detection to resolution with a unified investigation workflow. Graylog Security allows you to instantly generate investigation reports, providing key findings and suggesting next steps.
By using Graylog as a centralized incident management solution, you can search for answers, collect evidence, and collaborate across teams for improved incident remediation processes.
To see how Graylog can uplevel your incident remediation capability contact us today.