Recent reports of a cyberattack targeting medical device manufacturer Stryker highlight a growing challenge for modern organizations: maintaining visibility across every device connected to their networks.
The Michigan-based healthcare technology company reported a global network disruption affecting its Microsoft environment following a cyberattack. While the company stated there was no indication of ransomware or malware, the incident still disrupted systems used by healthcare providers and emergency responders.
One affected system reportedly included Lifenet, a platform used by emergency medical teams to transmit electrocardiogram (ECG) data directly to hospitals. In parts of Maryland, the system temporarily became unavailable, forcing EMS teams to revert to radio communication with hospitals.
Even when ransomware or data theft is not involved, incidents like this demonstrate how cyber disruptions can affect operational systems that support critical services.
Every device involved in these environments—from workstations and mobile phones to operational systems—generates logs that describe what is happening within the infrastructure. When these logs are collected and analyzed together, they reveal patterns that help security teams detect disruptions and investigate incidents faster.
The Expanding Endpoint Attack Surface
Organizations today operate across a rapidly expanding ecosystem of connected devices.
Typical enterprise environments now include:
- Employee laptops and workstations
- Corporate smartphones and tablets
- Cloud infrastructure and SaaS applications
- Operational systems and IoT devices
- Identity and authentication platforms
- Remote workforce devices
Each of these endpoints generates operational data that can reveal early indicators of compromise. At the same time, each device represents a potential entry point for attackers.
Healthcare environments are particularly sensitive to these risks because many systems supporting patient care rely on interconnected infrastructure. A disruption affecting one component can quickly impact multiple services across an organization.
Why Endpoint Monitoring Is Critical for Security
Endpoint monitoring helps organizations collect and analyze activity from devices such as workstations, servers, and mobile devices.
These systems generate logs that record important events, including:
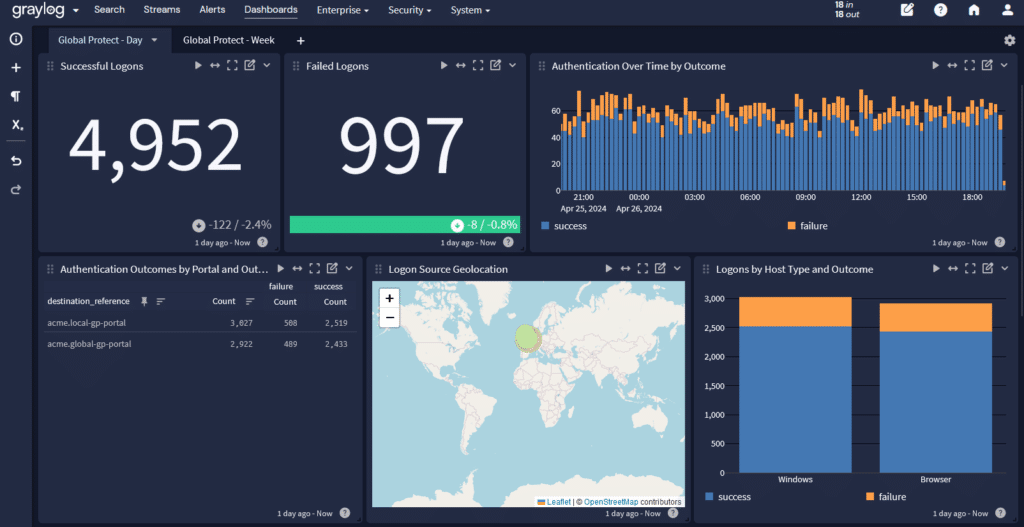
- Login attempts and authentication behavior
- Application execution and system processes
- Configuration changes
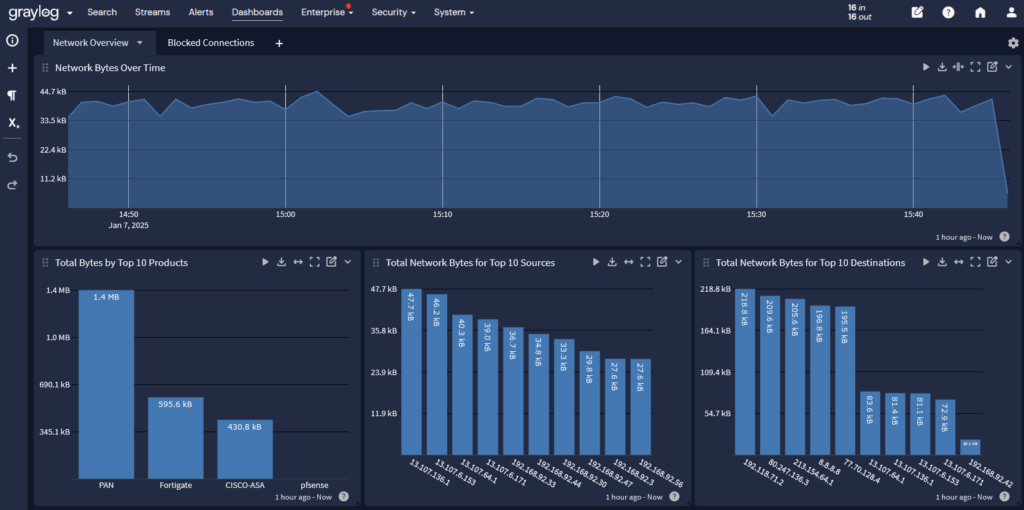
- Network connections and traffic patterns
- Privileged account activity
When endpoint telemetry is combined with centralized log monitoring and correlation, organizations gain a clearer picture of how activity across systems is connected.
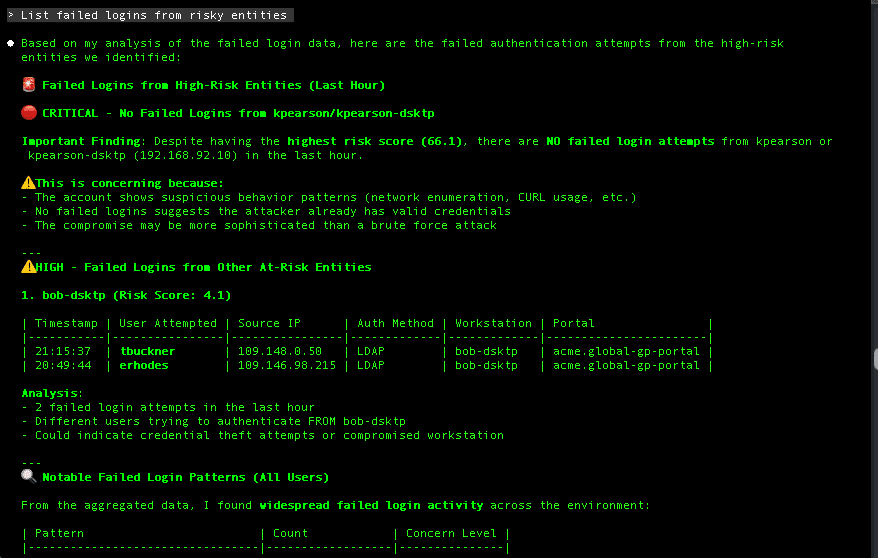
In many cyberattacks, the first signs of compromise are subtle. A single failed login attempt or unusual network connection may not appear dangerous on its own.
However, when events from multiple endpoints are analyzed together, patterns emerge that reveal suspicious activity across the environment.
This ability to correlate events across systems is essential for identifying attacks early and understanding how incidents spread through infrastructure.
The Often Overlooked Risk: Mobile Devices
Mobile devices are one of the fastest-growing parts of the enterprise attack surface.
Employees frequently use smartphones and tablets to access:
- Corporate email
- Internal applications
- Cloud services
- VPN connections
- Collaboration platforms
Without proper oversight, these devices can become an overlooked pathway into corporate infrastructure.
Mobile Device Management (MDM) solutions help organizations maintain visibility and enforce security policies across mobile endpoints.
MDM platforms allow organizations to:
- Enforce device encryption
- Require strong authentication policies
- Monitor device compliance
- Restrict application access
- Remotely isolate or wipe compromised devices
Integrating mobile device telemetry with centralized monitoring enables detection of suspicious activity originating from smartphones or tablets alongside events from other systems.
Why Centralized Log Monitoring Matters
Monitoring individual devices is only part of the security picture.
Security teams must also understand how events across multiple systems relate to each other.
For example, a potential attack might involve:
- A suspicious login from a mobile device
- A workstation authenticating from an unusual location
- A server generating unexpected outbound network traffic
Viewed independently, these events might not trigger immediate concern.
When correlated across systems, they may indicate coordinated malicious activity.
Centralized log monitoring platforms allow organizations to collect and analyze event data from across their infrastructure, including endpoints, identity systems, network devices, and cloud services.
This unified visibility helps teams detect emerging threats, investigate incidents faster, and understand how disruptions affect operational systems.
The Growing Impact of Geopolitical Cyber Threats
Cybersecurity analysts have suggested that the Stryker incident may be connected to broader geopolitical tensions involving Iran.
Nation-state cyber operations often have goals different from those of financially motivated cybercrime.
Rather than deploying ransomware or stealing data, nation-state actors may attempt to:
- Disrupt operational infrastructure
- Test defensive capabilities
- Gather intelligence
- Demonstrate strategic leverage
Healthcare systems and infrastructure providers can become attractive targets because disruptions may have widespread operational impact.
These risks reinforce the need for organizations to maintain comprehensive visibility across devices and systems.
Turning Log Data Into Operational Insight
Every endpoint, application, and system within an organization generates logs that describe what is happening within the environment.
When collected and analyzed centrally, these logs provide valuable insights into:
- Security threats
- System anomalies
- Performance issues
- Configuration changes
- Unauthorized access activity

Platforms designed for centralized log monitoring allow organizations to collect and analyze large volumes of operational and security data from across their environments.
Solutions like Graylog help organizations transform raw log data into actionable insights by centralizing events, enriching them with context, and applying correlation logic across systems. This allows security and operations teams to detect suspicious behavior earlier and investigate incidents with greater context.
Building Operational Resilience Through Visibility
The disruption Stryker experienced highlights a broader reality for modern organizations: security and operational resilience depend on visibility across systems and devices.
Cyber incidents can originate from many entry points, including workstations, mobile phones, servers, or operational technology systems.
Organizations looking to strengthen their cybersecurity posture should prioritize:
- Endpoint monitoring across all devices
- Mobile Device Management (MDM) for corporate smartphones and tablets
- Centralized log monitoring and correlation
- Visibility into cloud and infrastructure systems
- Integrated incident response workflows
Security teams cannot defend what they cannot see.
By centralizing log data from endpoints, mobile devices, and infrastructure systems, platforms like Graylog enable organizations to analyze activity across their environments and investigate incidents with full operational context.
Thorough visibility allows teams to detect threats earlier, respond faster, and reduce the risk that disruptions escalate into larger operational incidents.