Defending against security threats is a full-time job. The question is: Whose job is it?
Our cybersecurity landscape is in constant flux, with more users having increased access to corporate data, assets, APIs, and other entry points into the organization. With nearly 80% of senior IT and security leaders thinking they lack sufficient protection against cyberattacks, there’s this constant feeling of being in a perpetual marathon of keeping security strategy, tactics, and accountability aligned.
As our expert panel discussed in this webinar, there is no single tool or concept that has a greater impact on your overall cyber landscape than working together as a team. Building off our recommendations to bridge cybersecurity and security hygiene, here we’ll discuss why teamwork matters and offer some ideas to get the collaboration ball rolling.
“Cyber security is no longer the preserve of the IT department alone, noted Deborah Petterson, deputy director for private sector critical national infrastructure at the National Cyber Security Centre (NCSC). Rather, she said, it had become a ‘team sport’ that required the involvement and engagement of all levels of a business.”
- “Why cyber security has become a ‘team sport’”, New Statesman
SECURITY OWNERSHIP: FROM FRENEMIES TO FRIENDS
Cybersecurity and IT teams are traditionally given strong mandates and big responsibilities to protect their organizations. What they lack is the authority to implement them, especially within development teams. Without buy-in from everyone, down to the employees on the front lines of corporate systems, there will always be gaps in security that hackers have proven themselves to take advantage of (consider that 88% of data breaches are caused by human error).
You can deploy all the security tools you want but if the people aren’t on board and fully invested in protecting their own, a breach is only inevitable. Even if your organization achieves a sufficient level of compliance, that’s really only one step above negligence — it’s not actually true security. Compliance is an outcome of security but not the whole picture.
Whether you’re just starting to implement cybersecurity protocols or are moving towards a full Zero Trust model, it’s really about building a culture of security and cyber hygiene within your organization.
It’s not an easy process and some of the barriers include:
- Not knowing about cybersecurity itself – it’s impossible for an employee to know good security hygiene habits if they don’t know what they are, or for an HR employee to deliver security training if they’re not cyber savvy themselves. The good thing is that there are many resources out there to get up to cybersecurity speed, from Udemy to LinkedIn, and plenty of third-party security training companies for larger enterprises.
- Perceiving the costs as too high – it’s hard enough for a CISO to convince their executive to commit more resources towards cybersecurity, let alone a DevOps engineer to convince their team lead. The path to success usually lies in speaking the language of leadership: Preventing risks and maximizing return on investment. With the average data breach costing $4.24 million, it pays to pay attention.
- “It’s not my problem” – some people just don’t want to take another training course or use multi-factor authentication on their phone, relying on the IT team to “do their job.” This is where relationship-building and trust become critically important, helping users understand that organizational security is only as strong as the people practicing it.
START AT THE TOP
Work with the C-suite to understand cybersecurity goals, align tactics with business strategy, deploy analytics tools, and create a charter for your security organization. Showing real numbers and real examples of data breaches helps make the case, as does educating on and reinforcing security requirements placed on the organization by industry regulators, customer expectations, and competitive table stakes.
If you don’t have access to executives, start with your own manager and get them onboard to work upwards.
1. ENGAGE EMPLOYEES REGULARLY
Building or transforming culture requires good marketing skills, treating each business unit as a customer that needs to have security both understandable and relatable. Communicating a clear set of goals, explaining trends, and showcasing successes keeps everyone engaged with security far past their training sessions. It also empowers them to make better decisions as security is kept top of mind, rather than an afterthought.
Like a product or service, think of your business units as customers and answer these questions to develop a security engagement plan:
- How will you market your cybersecurity program?
- How will you support employees to grow adoption and retention?
- How will you prove value back to them for the effort they’re spending?
2. KEEP LEADERSHIP UP TO DATE
It’s always good to tell leaders what their investments are achieving – weak communication is a big reason for the lack of trust between the C-suite and the security function.
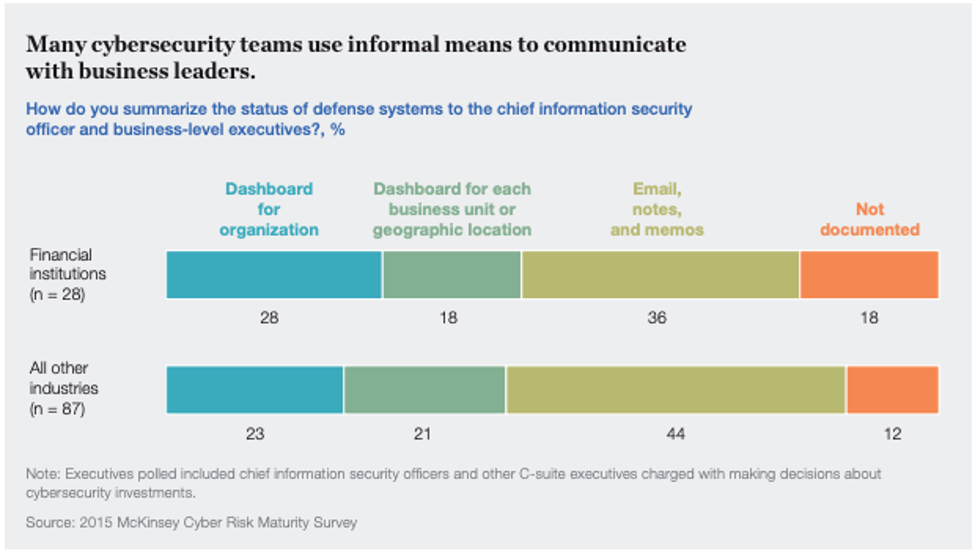
“In about half of the companies we studied, there was little to no formal documentation shared by the cyber function with the C-suite about the status of their defense systems; many companies relied instead on occasional emails, memos, and notes.”
- Perspectives on transforming cybersecurity, McKinsey & Company (PDF)

Regular reporting (KPIs, metrics, priorities, gaps) to help leaders see what’s working and not working helps you maintain a commitment to security that flows throughout the organization.
3. MAKE IT FUN
No one cares about security if it’s perceived as boring or makes them feel inadequate, especially when it comes to training. Adding gamification to phishing awareness training and role-playing during classroom sessions helps both adoption and learning retention. Avoiding fear, finger pointing, and negative talk is equally important in growing and maintaining a culture that people want to be a part of.
Improving security is more than hiring CISM and CISSP credentials, it’s putting the strategy and tactics in place to make it a team sport. It means defining goals that the entire organization understands and executing a roadmap that everyone can reach. Treating each employee as a partner, and not a compliance checkbox, leads to a more cyber-conscious culture and strengthens the organization as a whole.
For more on the advantages of team collaboration and examples of real tactics, watch this panel webinar: Security Analytics is a Team Sport