Log management maturity and cybersecurity maturity often mirror one another. In today’s highly connected world, companies need to live with risk. Organizations need to balance the risks they’re willing to accept and compare that to the amount of money they’re willing to spend.
Centralized log management is often a way to get the security monitoring that you need. As you mature your log management strategy, you’ll often find that you mature your security posture as well.
Level 1: Collecting the Right Information for Security Visibility
The first step to gaining visibility is collecting logs and bringing everything together in a single location. At this point, you’re trying to create an authoritative source for all security monitoring and log management.
This process gets you to the first level of both log management and cybersecurity maturity. You’re now collecting information as part of gaining visibility.
The problem for many security teams is that they’re getting too many log messages, not using alerting capabilities, and don’t use dashboards or reporting functions. This is when you know that you’re ready to level up your practices, scale back on the noise, and focus on the information you really need.
Start with the Basics
The first logs that you want your log management solution to ingest are the basis. This means starting with your on-premises and edge security devices including:
- firewalls
- Proxies
- mail gateways
- internet cables
- Intrusion Detection Systems (IDS)
- Intrusion Prevention Systems (IPS),
- Active Directory
- Terminal Access Controller Access-Control System (TACACS)
- Antivirus
Basically, you want to think about all the different on-premises and remote connections that require authentication and authorization.
Complement with Complexity
Now that you’re collecting the basic information, you can start complementing this with additional data that can add depth to your monitoring.
Some considerations should include:
- Server infrastructure logging
- Operating system logs, including Windows Application System and Security Logs, Linux host log, and the Linux audit log
- Agents, like the ones for servers
Once you start collecting all this information, you need to move on to the parsing and normalization process.
Know the Use Cases
Data in its raw form can often become overwhelming or “noisy.” The use cases are the security questions that you want your log management solution to answer.If you don’t know the use cases, you want to start generating a spreadsheet that helps you outline the data sources and the potential security risks.
When you know these, you can move from raw data to parsed and normalized information because you know how you want to aggregate and correlate data. Now you can detail the log sources that determine your parsing and normalization needs by listing all the data that you’re going to collect, down to the individual sources and log files.
Level 2: Parsing and Normalizing Data for Security Alerting
The parsing and normalization decisions help you gain the visibility you need by defining the data included in your alerts. Without parsing and normalization, you can’t have any correlated alarms.
If you don’t have the data formatted in the same way, your centralized log management solution won’t be able to answer the questions you need to ask. Consider the following differences for username fields:
- Windows: “username”, all one word
- Linux: user_name.
By normalizing the data, your centralized log management solution compares both of these fields by reformatting them to be the same.
Now, you can start to pull out some interesting information, gain value from the solution, and highlight environments that need better cybersecurity hygiene.
Set the Alerts
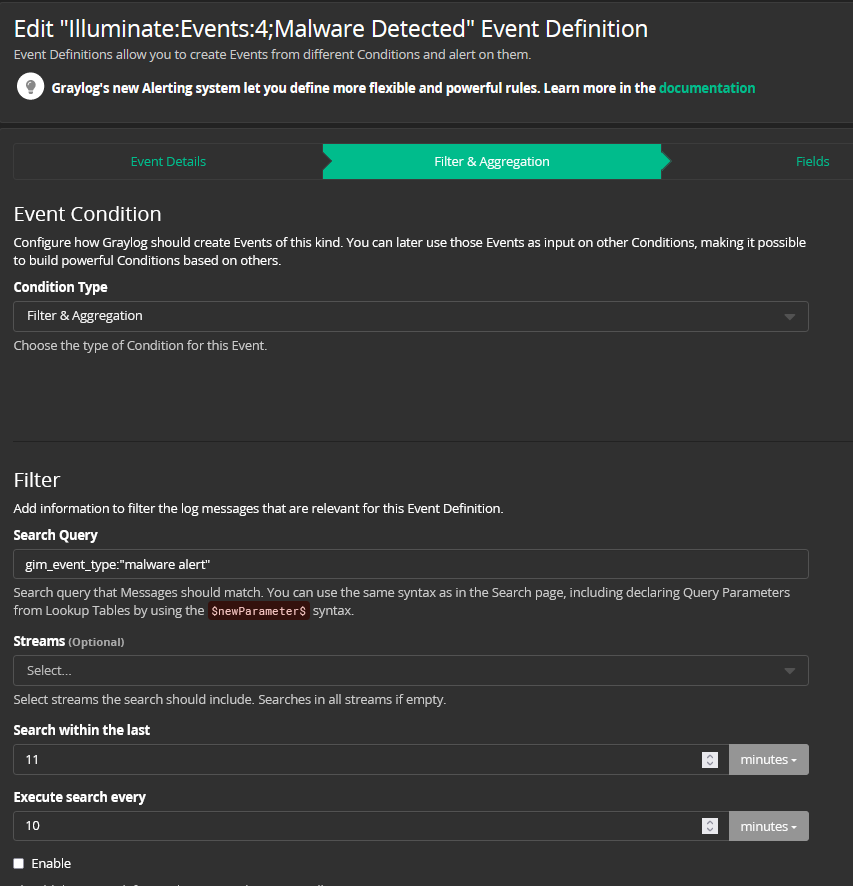
Now that the data is collected, aggregated, parsed, and normalized, you can set alerts. This is where your security and log management maturity become more intertwined.
For example, now you’re not just collecting all the information, you’re asking important security questions.
You might set an alert for things like:
- Monitoring multiple users in an admin group
- Malware detected on devices
- Firewall policy changes


You know you’re ready to level up again once you start seeing things in your environment that require a response.
Level 3: Creating Correlated Searches and Dashboards for Security Monitoring
Now that you’re parsing out the information, some fields may remain blank or an audit may find a discrepancy. The good news is that while you might need to do a little cleanup, you’re simultaneously maturing your security posture.
The realization that you’re missing information you want and need means that your centralized log management tool is giving you the visibility you didn’t have before.
Now that you’re building out alarms and questions, you’re iterating your data collection, refining the parsing and normalization processes, and fine-tuning your alerts or building out dashboards.
All of these processes mature your log management strategy and cybersecurity posture. You’re maturing your log management strategy by looking at the data you need and being purposeful. At the same time, you’re maturing your security posture by using dashboards and getting higher fidelity alerts that help your security team respond more effectively.

Level 4: Correlating Data and Building Automation for Proactive Security
Now that your team is getting the alerts they need to respond to threats more rapidly, you want to mature your log management and security postures by building in automation. In security, you want to move toward a proactive posture. If you remain in a reactive position, you’re only responding to threats after they happen, which means the threat actors have already infiltrated your environment.
First, you can set up alerts for common problems that everyone has. Once you’ve done that, you continue to iterate and refine, building out alerts around security gaps, and reviewing a potential event’s risk is worth the cost of remediation.
When your centralized log management solution has security analytics, you add another automation layer. Machine learning automates processes like:
- Defining baselines
- Risk modeling
- Cloud access monitoring
With threat intelligence, you can automate activities like threat hunting to reduce employee time spent on proactive security activities. Ultimately, this reduces the total cost of ownership and increases the return on investment.


Use Case: Admin Account Logins Correlated to Windows Events
Administrator accounts are, by nature, inherently risky because the users have nearly unfettered access across your environment. Running a search on admin accounts will always provide information about what the user is doing. When reviewed alone, you’re not going to get a lot of insight into risk.
You can refine the admin access reviews by looking at Windows Events. Then, you get visibility into:
- when admins are logging off,
- when account logins failed, and
- when admins logged into their accounts.
From here, you can start to build out visualizations and tables. For example, if you see a single failed admin account login, that could just mean a mistyped password. However, if you see 200 failed logins in the last hour, you want to investigate further. This could be an attempt at a brute force or dictionary attack which places sensitive information at risk.
Graylog’s dashboards enable security analysts to scan data for enhanced risk visibility. We start to ask questions about data. This level of automation enables security teams to analyze data more rapidly and take proactive steps to mitigate potential risks. Even if it turns out that the logins were unrelated to a brute force attack, your team is doing everything it can to detect anomalous activity and prevent a data security incident.
Level 5: Iterating with Automation to Continuously Improve Security
Now that you’ve added some automation for proactive security monitoring and have visibility into risks, you’re ready to level up again. The fundamental rule for both security and log management is: iteration enables continuous improvement.
What does this look like? This level is where you’re starting to really dig into your own organization’s needs:
- Integrating with other tools like service desk tools reduces the time analysts spend copying alarm information from one screen and pasting into a ticket
- Fine-tuning alerts can reduce alert fatigue
- Taking strong manual processes and finding ways to automate them can save time
- Engaging in a gap assessment and creating alerts around detected weaknesses
- Adding more log sources or different log sources
Use Case: Integrating with Ticketing For Effective Threat Hunting
When you integrate ticketing into your threat hunting processes, you can make them mowith no way to measure value. If the team doesn’t detect something, then it can look like they’re not really doing anything. If they do find something, then they’re heroes.
Meanwhile, responding to the weaknesses found during the process is where it starts to erode. The people responsible for fixing the gap have so many things on their plate that this as-yet-unexploited vulnerability becomes the lowest priority on the To Do List.
Integrating your threat hunting with your ticketing system means that your team can align alert types with risk level. Your threat hunting team can triage vulnerabilities, enabling your IT team to expedite responses. This gives you a way to measure the threat hunting team’s value rather than being viewed as an IT team burden.
Use Case: Integrating with Ticketing for Enhance SLA
Integrating with ticketing systems also provides value for security teams who need to meet internal performance metrics.
An organization may be automating alarms into a service desk to create a trouble ticket. Then, the analyst will have an SLA against that trouble ticket, requiring a response to each alarm within a certain timeframe. If they don’t respond within the required timeframe, they can be in breach of their SLAs or performance metrics.
For example, many support organizations have different tiers. When the ticket comes in, the IT team needs to manage it. The SLA timing requirement might be 30 minutes. Maturing log management tool configurations solves these problems in two different ways:
- Better prioritization: higher fidelity alerts mean that analysts can better prioritize high risk activities which means the help desk can route them more efficiently
- Fewer tickets: higher fidelity alerts reduce the overall number of alerts by correlating data more effectively, ultimately reducing the burdens IT teams face.
Graylog Security: An Out-of-The-Box Log Management Strategy for Cybersecurity
Graylog Security provides the content you need to optimize your log management strategy and align it with IT operations. Security and IT teams can both use our lightning-fast search capabilities to meet their objectives, whether it’s investigating a security incident or meeting SLAs. Built on the Graylog platform, Graylog Security combines our intuitive user interface with Security Analytics and Anomaly Detection capabilities so that everyone’s job becomes easier.
No matter what your security or log management maturity level is, Graylog’s cloud-native capabilities ensure that you start getting valuable data from your logs faster. Your teams get the correlation and alerting they need to reduce alert fatigue while being able to automate activities like threat hunting.