Data’s role in business processes continues to evolve. Today, organizations collect, store, process, and transmit more personal data than ever before, and legislative bodies respond by updating privacy laws.
Türkce çevirisi için bu linke tıklayınız.
In 2016, Turkey passed the first iteration of its Personal Data Protection Law number 6698 (PDPL), which also established the Kişisel Verileri Koruma Kurumu (KVKK), the country’s data protection authority. In 2021, the Turkish government indicated its plan to update the law so that its data protection requirements would align more clearly with the General Data Protection Regulation (GDPR). However, currently, the PDPL remains in its 2016 state with amendments expected over the next few years.
Companies can use centralized log management to help them comply with Turkey’s PDPL by leveraging security analytics to help mitigate data breach risks.
What is the Personal Data Protection Law (PDPL)?
Ratified on March 24, 2016, the Turkish PDPL aims to protect people’s fundamental privacy rights when companies process personal data. The law defines data subjects’ rights and companies’ obligations to protect those rights.
The Turkish PDPL applies to two types of organizations:
- Data Controllers: anyone determining how and why personal data is processed, who establishes and manages the data filing system used to structure data according to specific criteria
- Data Processors: anyone processing data on a data controller’s behalf according to the data filing system
Chapter 6 established the Personal Data Protection Authority (KVKK), defining its duties as follows:
- Monitor the regulatory landscape to make evaluations and recommendations or conduct research and investigations
- Monitor and evaluate international developments related to personal data
- Work with public and private organizations
- Publish an annual activity report
Additionally, Article 21 established the Personal Data Protection Board, defining its duties in Article 22 as:
- Ensuring that personal data processing complies with the fundamental rights and freedoms
- Responding to and investigating privacy violation complaints
- Determining adequate measure for processing special categories of data
- Maintaining the Data Controllers’ Registry
- Carrying out regulatory acts, including determining data security requirements and matters concerning data controller duties, powers, and responsibilities
- Imposing administrative sanctions
- Delivering opinions about draft legislation containing provisions about personal data
What data and activities does the PDPL cover?
As with many privacy laws, the PDPL defines personal data as any information relating to an identified or identifiable natural person. However, it also includes the following categories of “special categories” of personal data:
- Race
- Ethnic origin
- Political opinion
- Philosophical belief
- Religion, religious sect, or other belief
- Appearance
- Membership to associations, foundations, or trade-unions,
- Health and sexual life information
- Criminal convictions and security measures
- Biometric and genetic data
The PDPL defines data subjects’ personal data as “any information relating to an identified or identifiable natural person.” Processing of personal data includes manual or automated operations that include:
- Collection
- Recording
- Storage
- Protection
- Alteration
- Adaptation
- Disclosure
- Transfer
- Retrieval
- Making available for collection or categorization
- Preventing use of data
What are key provisions contained in Turkey’s Personal Data Protection Law?
At a high level, the PDPL outlines the five general principles that companies must comply with when processing personal data:
- Lawfulness and fairness
- Maintaining accurate and up-to-date data
- Processing for specified, explicit, and legitimate purposes
- Being relevant, limited, and proportionate to the reason for processing
- Storing data for only as long as required by law or the reason for processing it in the first place
Condition for processing personal data
When processing personal data, companies need to gain explicit consent from the data subject.
The PDPL defines the following exceptions to the explicit consent requirement:
- Expressly allowed by law
- Necessary to protect life or physical integrity
- Between parties of a contract and directly related to the contract’s establishment or performance
- Necessary to comply with data controller’s legal obligation
- Personal data that the data subject makes public
- Necessary to establish, exercise, or protect a right
- Necessary to the data controller’s legitimate interests without violating the data subject’s fundamental rights and freedoms
The law prohibits processing of most special categories of personal data without obtaining data subjects’ explicit consent.
Erasure, destruction, or anonymization of personal data
Data subjects have the right to ask data controllers to erase, destroy, or anonymize any personal data they collect, store, or process.
Transfer of personal data domestically and abroad
Unless transferring data under one of the law’s exceptions, data controllers and data processors cannot transfer personal data at home or abroad without gaining the data subject’s explicit consent.
When transferring data outside Turkey, companies must ensure that the country provides adequate protections or that they obtain written commitment for adequate protections as approved by the KVKK.
Informed Consent
Data controllers must inform data subjects that they are collecting personal data and provide:
- The purpose of processing
- To whom and for which purposes they transfer data
- Method and legal basis for collecting personal data
Data subjects have the right to ask the data controllers:
- Whether or not they process personal data
- Whether their personal data has been processed
- Why they process data and whether it’s been used only for this purpose
- About any domestic or international personal data transfers
- Have incomplete or inaccurate personal data updated
- Have personal data erased or destroyed
- What third-parties received transferred data
- About any decisions and object to them when data analysis is solely done through automated systems
- For compensation for damages arising from unlawful data processing
Data Security
Data controllers must implement appropriate data security using technical and organizational controls for personal data to :
- Prevent unlawful processing
- Prevent unlawful access
- Ensure protection
Data controllers share data security responsibilities with their data processors so must carry out the necessary audits to ensure data processors’ compliance.
Data controllers are responsible for notifying data subjects and the KVKK when a data breach occurs.
Data Controllers’ Registry
Before processing personal data, companies must register with the Data Controllers’ Registry and provide:
- Data controller or representative identity and address
- Purpose for processing personal data
- Groups of data subjects and the data categories being processed
- Recipients of data transfers
- Personal data that may be sent outside Turkey
- Data security measures
- Maximum storage period
Fines and penalties
Crimes concerning personal data fall under Articles 135 to 140 of Turkish Penal Code No. 5237 of 26/9/2004. Specifically, companies that fail to erase or anonymize personal data are subject to Article 138 of Law No. 5237.
Additionally, the PDPL outlines the following administrative fines for compliance violations:
- Failure to inform data subjects: 5.000 to 100.000 TL
- Failure to provide adequate data security: 15.000 to 1.000.000 TL
- Failure to remediate issues identified by the KVKK: 25.000 to 1.000.000 TL
- Failure to register with the Data Controllers’ Registry: 000 to 1.000.000 TL
Data Breach Notification Requirements
In 2019, the Personal Data Protection Board (the Board) published Decision No. 2019/10 of 24.01.2019 about Procedures and Principles of Personal Data Breach Notification (Decision No. 2019/10). In Decision 2019/10 the Board outlined the following notification timelines:
- Data controllers shall notify the Board without delay and not later than 72 hours after becoming aware of the breach.
- Notifications not made by data controllers within 72 hours should include reasons for the delay
- Data processors shall notify data controllers about incidents arising through unlawful methods.
Centralized Log Management for Compliance with Turkish Personal Data Protection Law
While the PDPL may not provide technical details, some of the Board Decisions offer insights into how it reviews incidents and applies administrative fines.
In 2019, the Board fined several organizations and published decisions explaining its reasons, including:
- Board Decision Decision No. 2019/143 on Marriott International Inc.: Web event logs showing unauthorized access as early as 2014 indicated a lack of technical and administrative measures.
- Board Decision No. 2019/269 on Facebook: Inability to detect and remediate the vulnerability during the testing phase allowed it to remain for fourteen months, indicating a lack of technical and administrative measures.
- Board Decision No. 2019/144 on Cathay Pasific Airway: Two month span between initiation of suspicious activity and detection of suspicious activity indicated a lack of monitoring and controls.
Using a centralized log management solution with security analytics, companies can comply with the current iteration of the PDPL while implementing robust security monitoring processes that enable compliance with future iterations of the law.
When paired with security analytics, centralized log management streamlines security monitoring by providing visibility into:
- User access
- Network security
- Endpoint security
- Vulnerability and patch management
- Data exfiltration/data loss
Further, organizations that incorporate user and entity behavior analytics (UEBA) into their monitoring gain capabilities like:
- Proactive threat hunting
- High-fidelity alerts for advanced detection capabilities
- Rapid vulnerability remediation
- Lightning fast incident investigation
Access Monitoring
In a complex environment, centralized log management solutions enable robust access monitoring when paired with UEBA and identity and access management (IAM) tools.
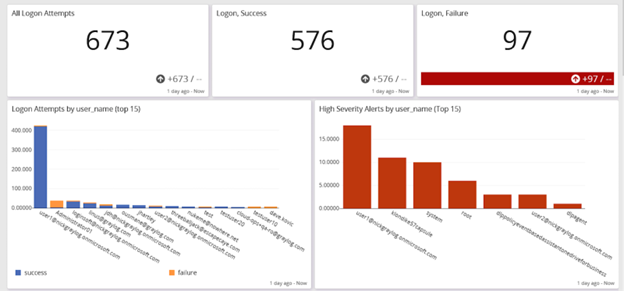
With these embedded analytics, you can manage security issues like:
- Privileged access management (PAM)
- Password policy compliance
- Abnormal privilege escalation
- Time spent accessing a resource
- Brute force attack detection
Network Security
By correlating and analyzing data generated by various network security monitoring tools, centralized log management enables you to create high-fidelity alerts to detect suspicious behavior that might indicate a security incident.
For example, since firewalls provide insight into suspicious traffic, like data traveling to a cybercriminal-controlled server, combining that data with your intrusion detection system (IDS)/intrusion prevention system (IPS) enables you to monitor for evasion techniques.


After identifying normal network traffic baselines, you can use security analytics to implement better detections or abnormal activity.


Data Exfiltration
Increasingly, ransomware and malware attacks steal data, so monitoring systems for data exfiltration is critical to detecting incidents quickly.
To create high-fidelity alerts, you can build dashboards that incorporate security analytics and threat intelligence. When the centralized log management solution includes lightning-fast investigation capabilities, you can reduce compliance violation risks by meeting the 72-hour timeline.
With network monitoring, antivirus logs, and UEBA, you can create detection rules to identify anomalous data downloads that indicate a potential incident.

Incident response and automated threat hunting
To mature your incident investigation and response program, you can use rapid research and proactive threat hunting for more robust processes.
By creating queries using parameters, you can optimize searches for real-time insights and answers. Instead of searching for specific values, parameterized searches give you the flexibility you need to automated advanced threat hunting, helping you gain visibility into:
- Abnormal user access to sensitive information
- Abnormal time of day and location of access
- High volumes of files accessed
- Higher than normal CPU, memory, or disk utilization
- Higher than normal network traffic
Compliance and post-incident reporting
When you can create dashboards in your centralized log management solution, you can use the visualizations to give people an easy-to-digest report that shares deeply technical information using charts or graphs so the security incident evaluation makes sense to them.
For example, you can build out dashboards that provide reports showing:
- Start of incident: when logs documented changes
- Incident activities: what types of changes the logs documented to highlight what the threat actor tried to do
- Containment/Eradication: when logs stop reporting the activities indicating the threat actor is no longer acting in the system
Graylog Security: Future-Proof Compliance with Security Analytics
With Graylog Security’s analytics and anomaly detection capabilities, you can create a security and compliance program that enables you to meet current PDPL requirements and prepare for future ones. Graylog Security provides prebuilt search templates, dashboards, correlated alerts, and dynamic look-up tables so that you can accelerate your security and compliance programs with one cost-effective solution.
Using our high-fidelity detections and lightning-fast search capabilities, you can rapidly investigate incidents with our intuitive user interface. Graylog Security gives you all the functionality you need to protect data and document your compliance activities.
To see how Graylog Security can help you comply with the Turkish PDPL, contact us today.