Decree No. 2009-834 established ANSSI (Agence nationale de la sécurité des systèmes d’information) as the National Cybersecurity Agency of France in 2009. In 2013, Article 22 of the Military Programming Law defined ANSSI’s functions and responsibilities, giving the agency regulatory and enforcement powers. Further, ANSSI is France’s primary point of contact with the larger European Union (EU) Network and Information Systems (NIS) Directive, with Decree No. 2018-384 implementing these requirements.
In 2022, France hosted the CSIRTs Network, CyCLONe, and NIS Cooperation Group where Member States agreed on revisions to Directive on Security of Network and Information Systems (NIS2). Companies that need to comply with ANSSI requirements may want to understand how centralized log management can enable compliance with the current French regulatory framework for Critical Infrastructures Information Protection (CIIP Framework) and streamline compliance for changes arising from NIS2.
What is Critical Infrastructures Information Protection (CIIP Framework)?
The Critical Infrastructures Information Protection Framework (CIIP Framework) sets forth a series of security compliance requirements for cybersecurity service providers, operators of essential services (OES), and industry sector ministries. While focused on critical infrastructure, CIIP aligns with the original NIS Directive and likely enables organizations to navigate the changes that NIS2 will bring about.
In January 2014, the General Secretariat of Defense and National Security (SGDSN) published Instruction Generale Interministerielle Relating To The Safety Of Activities Of Vital Importance as an interministerial general instruction for all companies that fall within the definition of “vital importance.”
In May 2018, Decree No. 2018-382 (the Decree) set forth the French implementing rules for the NIST Directive specifying the risk management elements required for establishing a common level of network and information security. The Decree established a set of requirements for essential services that includes:
- Security rules
- Security incident notifications
- Security checks
Although not directly referenced by the Decree, the CIIP Framework enables organizations to achieve cybersecurity objectives aligned to the original NIS Directive. With NIS2 implementation rules on the horizon, understanding current CIIP compliance requirements and understanding gaps with NIS2 provides companies a potential roadmap.
Who does the French CIIP apply to?
CIIP outlines twelve sectors of “activity of vital importance,” or critical infrastructure:
- Civil State Activities (ACE)
- Judicial activities
- State Military Activities (AME)
- Feed
- Electronic, audiovisual, and information communications
- Energy
- Space and research
- Finances
- Water management
- Industry
- Health
- Transportation
What are CIIP Framework’s key provisions?
Operators of vital importance (OIV) must implement controls as required by the security system for activities of vital importance (SAIV) system framework. These plans should define and apply security measures that prioritize protection of points of vital importance (PIV) that include:
- Operator safety plans (PSO)
- Plans for protection of points of vital importance (PPP)
- External protection plans (PPE)
Each OIV must comply with the National Security Directive (DNS) that applies to its industry sector. While these may differ in some ways, the CIIP Framework creates similarities across all sectors so that businesses can cohesively protect data and systems. The coordinating sector minister will determine and notify a company of its OIV status.
In 2021, ANSSI published an update to its 2020 “Recommendations for the architecture of sensitive or Restricted Distribution information systems” document, outlining technical controls that organizations can use as part of their CIIP Framework compliance program.
Section 3.2 Le Plan De Securite D’opérateur (PSO)
OIV must develop and implement a PSO that complies with its sector DNS. A PSO must incorporate:
- A list of PIVs specifying the activity carried out at each point
- Risk analysis outlining reasons for identifying each PIV
Companies implement their PSOs through their defined security organization which includes their delegate for defense and security.
3.3. Le Point D’importance Vitale (PIV)
To classify as a PIV, something must meet the following CIIP Framework requirements:
- Establishment, facility or structure
- Damage, unavailability, or destruction arising from malicious intent, sabotage, or terrorism directly or indirectly risks:
- Military or economic security or survival
- Health or life
While OIVs are responsible for identifying PIVs, they should consider how to:
- Reduce scope by focusing on critical components
- Implement defense in depth strategies
Under this section, OIVs need to implement procedures for:
- Controlling access to PIVs (3.3.4)
- Modifying operating conditions or transferring a PIV (3.3.5)
3.5. Le Special Protection Plan (PPP)
A company’s PPP defines the internal safeguards that the company uses to:
- Defeat or delay threat actors
- Limit impact
- Facilitate business continuity or business recovery
The ANSSI guidelines outline the following minimum security protections that enable a company to implement and maintain a PPP:
- 2 Encryption: Using encryption appropriate to the data’s sensitivity level
- 3 Internal partitioning of the sensitive IS and hardening of systems: Placing assets with homogeneous security needs on the same network to block lateral communications across distributed resources, including servers
- 4 Marking: Marking structured and unstructured sensitive information and media storing sensitive information
- 5 Managing authentication and access rights: Enabling strong initial authentication, protecting authentication secrets, and managing logical access rights
- 6 Protection against malware: Installing anti-virus software on application servers, workstation, and interconnection media
- 7 Managing devices and removable media: Limiting and controlling removable media use, encouraging read-only media, using storage media decontamination solutions
- 1 Controlling sensitive IS workstations: Controlling installed software and its configurations, administering and updating equipment, blocking attacker lateral movement, protecting against theft
- 2 Connecting workstations to the network: Connecting sensitive resources on dedicated physical and logical networks, authenticating sensitive resources to the network
- 3 Workstation architecture: Using a dedicated sensitive user workstation, using a multi-level user workstation that leverages virtualization or containerism technologies, using a sensitive user workstation with remote access to the standard IS
- 4 Mobility: Protecting physical access to mobile devices, authenticating both users and devices when connecting to resources, encrypting traffic using Virtual Private Networks (VPNs), encrypting mobile storage devices, encryption network flows
- 5 Wireless networks: Partitioning wireless network from sensitive IS, preventing sensitive mobile access equipment from accessing public captive portals
- 3 Remote administration: securing remote administration using a VPN technology, controlling remote maintenance systems
3.6. Plan De Protection Externe (PPE)
A company’s PPE defines the organization’s plans for security:
- Monitoring
- Prevention
- Protection
- Response
The ANSSI guidelines offer insight into controls that organizations can use when developing their PPE, including:
- 4 Security maintenance (MCS): Defining and implementing a vulnerability and patch management program that includes deployment frequencies and testing procedures with critical updates deployed within one week and all other security updates within four weeks, isolating obsolete systems
- 5 Security logging and monitoring: collecting logs and retaining them for a period of twelve rolling months for security detection and investigation capabilities like:
- Triggering security alerts based on defined detection rules
- Improving alerts by reducing false positives
- Investigating suspicious events after the fact
4.1. Audit Interne Mene Par l’OIV
OIVs must engage in internal adults that assess PPP validity and may revise the PPP in response. OIVs control audit:
- Frequency
- Team composition
- Methodology
While OIVs do not need to send reports to administrative authorities, they should have them available for inspection.
4.2. Controles Par Les Prefets
Department prefects approve PPPs and draft PPEs. Additionally, they may engage in discretionary on-site PIV visits.
Centralized Log Management for ANSSI and CIIP Framework Compliance
When viewing ANSSI and the CIIP Framework through the lens of NIS2, companies should note that NIS2 implements strict security incident response and notification requirements. ANSSI offers several publications that address incident response, including its Crisis of cyber origin, the keys to operational and strategic management and Organizing a cyber crisis management exercise. However, when compared to NIS2, the current publications may need to be updated.
NIS2’s Article 23 “Reporting obligations” requires covered entities to provide notification as follows:
- 24 hour or less from detection: early warning including potential illegal acts, malicious acts, and impact
- 72 hours or less from detection: incident notification that updates the early warning and includes severity, impact, and indicators of compromise (IoCs)
- On-demand: responses to CSIRT or authority requests
- 1 month or less from incident notification: final report including detailed incident description
For companies currently using ANSSI’s publications or the CIIP Framework, the good news is that the updated publications already address many changes that NIS2 seeks to address, like risks arising from digital transformation.
As organizations prepare for NIS2 and changes to French compliance requirements, implementing centralized log management with security analytics can streamline the process by providing visibility into:
- User access
- Network security
- Endpoint security
- Vulnerability and patch management
- Data exfiltration/data loss
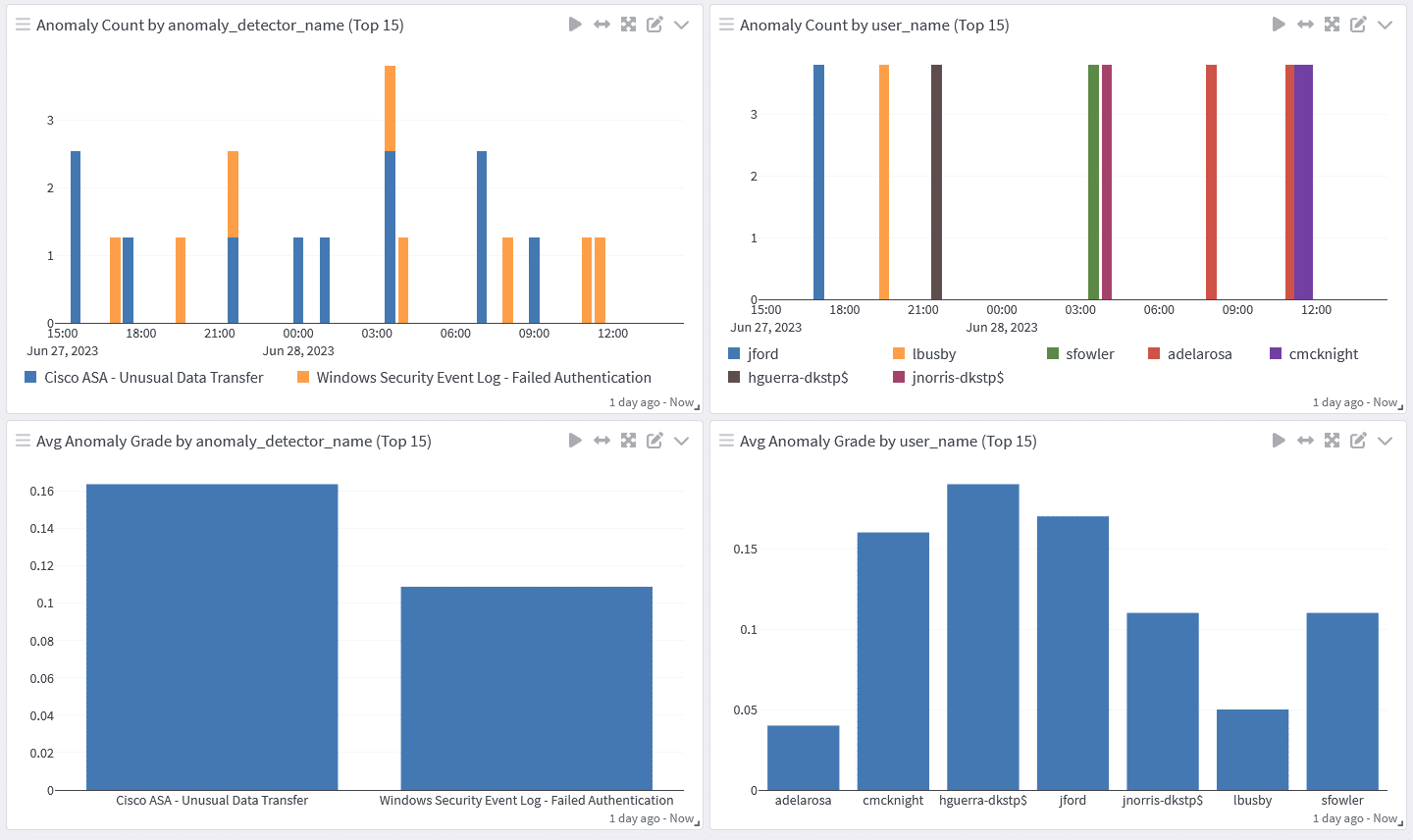
Pairing this visibility with user and entity behavior analytics (UEBA), you gain additional capabilities for:
- Proactive threat hunting
- High-fidelity alerts for advanced detection capabilities
- Rapid vulnerability remediation
- Lightning fast incident investigation
Monitoring Access
Even within a complex environment, pairing your centralized log management solutions identity and access monitoring with UEBA gives you robust access monitoring.
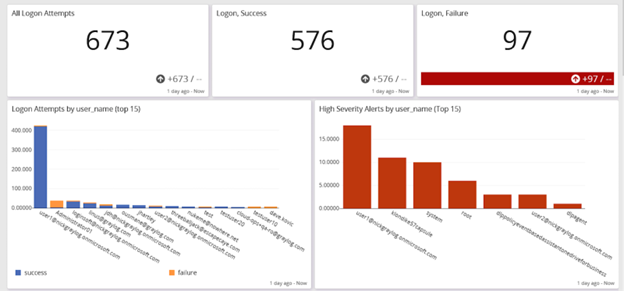
These embedded analytics enable you to manage security issues like:
- Privileged access management (PAM)
- Password policy compliance
- Abnormal privilege escalation
- Time spent accessing a resource
- Brute force attack detection
Network Security
With centralized log management, you can correlate and analyze data generated by multiple network security monitoring tools for high-fidelity alerts for suspicious behavior indicating a potential security incident.
By combining your firewall data with your intrusion detection system (IDS)/intrusion prevention system (IPS) monitoring for visibility into evasion techniques.
Your firewalls tools can provide insight into suspicious traffic, like data traveling to a cybercriminal-controlled server.
When correlating this with IDS/IPS data, you get a more comprehensive picture.
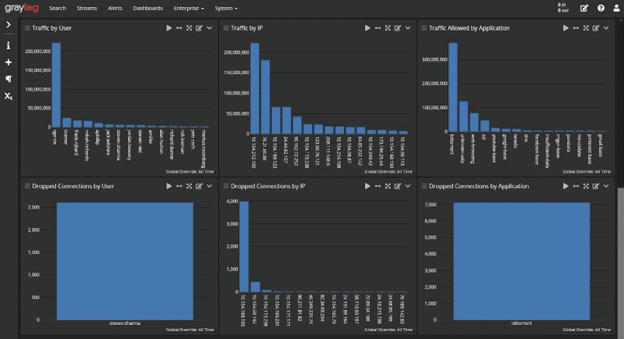

Bringing all of this together with security analytics, means that you have baselines that define normal network traffic so that you can implement better detections for abnormal activity.
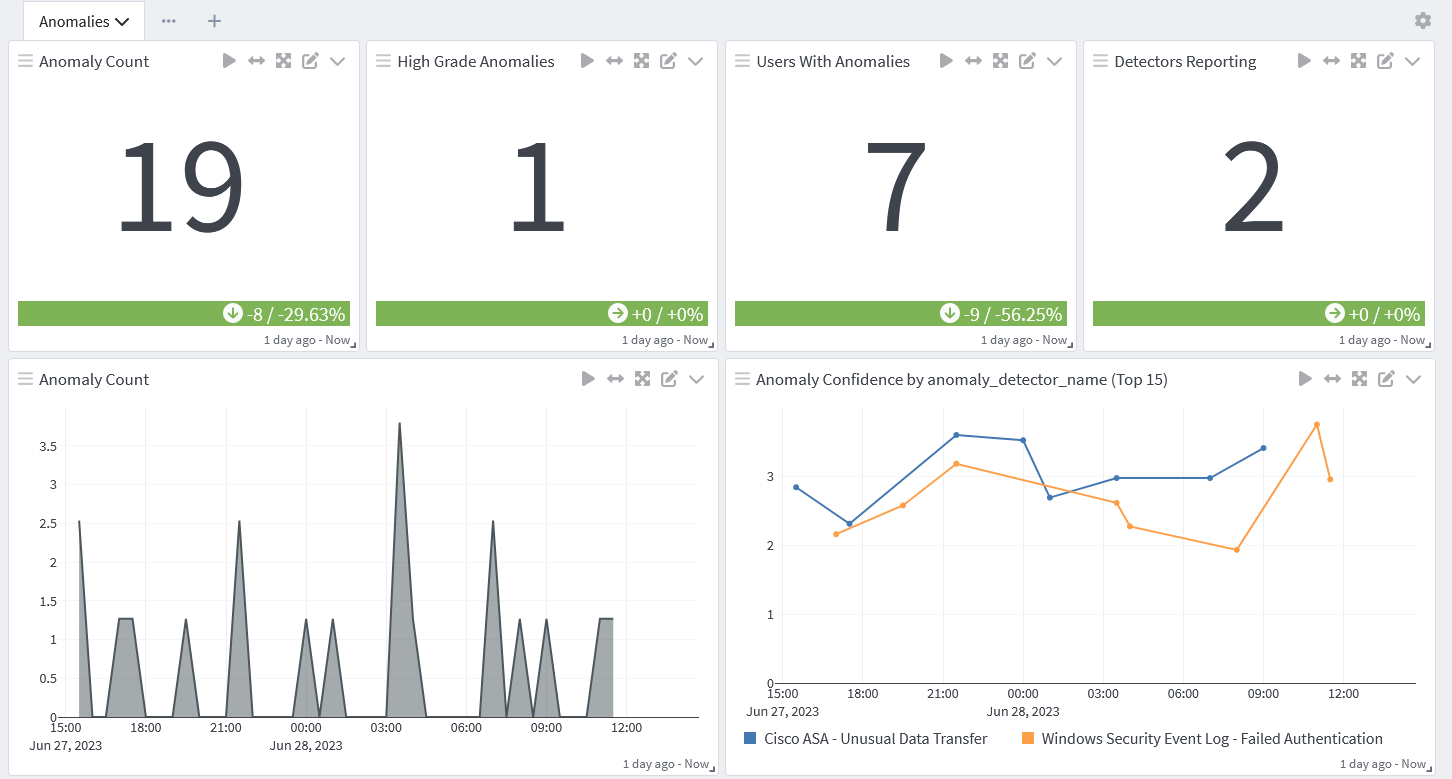
Data Exfiltration
As more ransomware and malware attacks seek to infiltrate systems and steal data, gaining visibility into data exfiltration becomes critical.
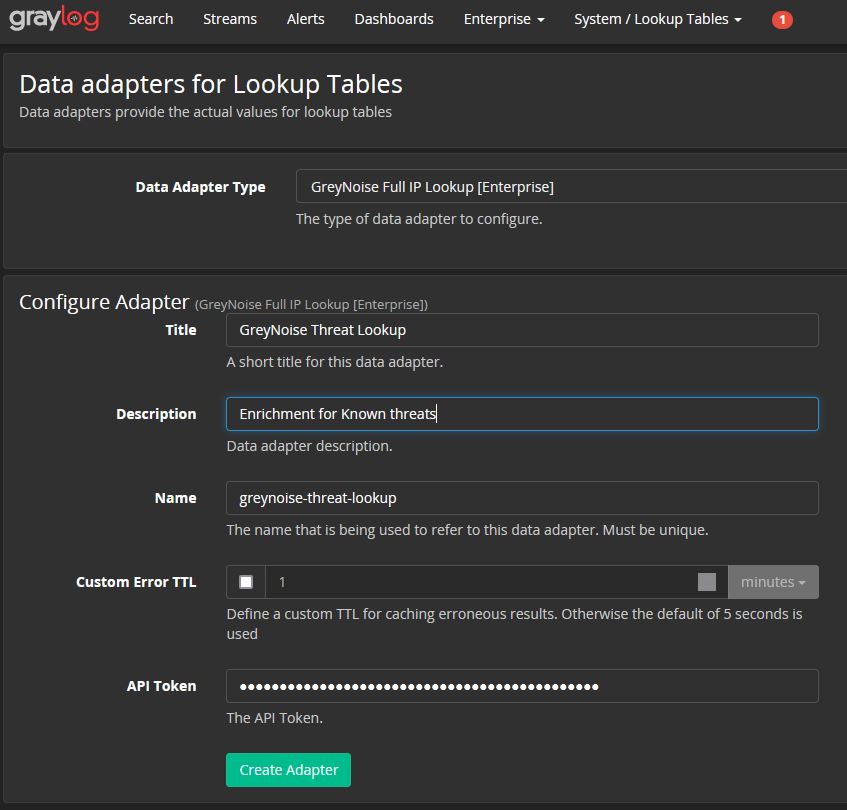
By building dashboards infused with security analytics, you can create high-fidelity alerts that incorporate threat intelligence. When combined with lightning-fast investigation and response capabilities, your centralized log management solution can help you meet these strict notification and reporting requirements.
By their powers combined, network monitoring, antivirus logs, and UEBA enables you to create detection rules for anomalous data downloads that indicate a potential incident.
Incident response and automated threat hunting
With rapid research and proactive threat hunting capabilities, you can mature your incident investigation and response program. In doing so, you can implement processes that help you meet the early warning, incident notification, and final reporting timelines.
For example, by creating queries using parameters rather than specific value, you can optimize your searches to gain real-time insights and answers.
With these parameterized searches, you can automate advanced threat hunting for visibility into:
- Abnormal user access to sensitive information
- Abnormal time of day and location of access
- High volumes of files accessed
- Higher than normal CPU, memory, or disk utilization
- Higher than normal network traffic
Compliance and post-incident reporting
With dashboards, you can create visualizations that provide people with the information they need in an easily digestible format. The dashboards enable you to aggregate the deep technical information with the charts or graphs that give people a security incident evaluation that makes sense to them.
With the right dashboard, you can provide visibility into:
- Start of incident: when logs documented changes
- Incident activities: what types of changes the logs documented to highlight what the threat actor tried to do
- Containment/Eradication: when logs stop reporting the activities indicating the threat actor is no longer acting in the system
Graylog Security: Security analytics for robust compliance
Graylog Security provides the analytics and anomaly detection capabilities you need while eliminating the complexity you don’t need. With our prebuilt search templates, dashboards, correlated alerts, and dynamic look-up tables, you can strengthen your security program and accelerate your compliance program with a cost-efficient solution.
With our intuitive user interface, you can create high-fidelity detections and investigate with our lightning-fast search capabilities to comply with increasingly strict notification requirements.
To see how Graylog Security can help you comply with ANSSI and the CIIP Framework, contact us today.