Governments, businesses, and society depend on reliable, functioning information and communication technology. However, increased severity of ransomware attacks and vulnerabilities in computer chips undermine these infrastructures. Further, as people adopt Internet of Things (IoT) devices, their inherent lack of security and ability to be aggregated into large, malicious bot networks increases these risks.
On April 23, 2021, Germany’s Bundestag passed the IT Security Act 2.0, which the Federal Council approved on May 7, 2021. By using centralized log management with security analytics, organizations can reduce the compliance costs associated with the IT Security Act 2.0.
What is the German IT Security Act 2.0?
The German IT Security Act 2.0 updates the 2015 “Act on increasing the security of IT systems” (German IT Security Act). The German IT Security Act expanded the original 1991 Act on the Federal Office for Information Security (BSI Act), ultimately enhancing the core tasks allocated to the Federal Office for Information Security (BSI) to include:
- Acting as the central reporting office for IT security across government and critical infrastructure
- Collecting, evaluating, storing, using, and processing protocol data and data arising at interfaces of federal communications technologies
- Passing on vulnerability information and warnings to affected bodies or the public
- Defining uniform and strict security standards for federal administration and government networks
- Auditing critical infrastructure security
- Examining IT products
- Analyzing interfaces and log data across federal networks
- Developing minimum IT standards across the federal administration
The German IT Security Act 2.0 further expanded the BSI’s core tasks to include:
- Establishing binding minimum security standards for detection, defense, and monitoring
- Establishing high-level security requirements for mobile networks
- Acting as a consumer protection body for IT security issues
- Acting as the National Cybersecurity Certification Authority (NCA)
What are the IT Security Act 2.0’s key changes and requirements?
The IT Security Act 2.0 builds upon the 2015 IT Security Act in response to the evolving threat landscape and expanding attack surface.
Some significant changes include the following:
- Definitions: Updated to reflect modern IT infrastructures, including new language about logging data, IT products, systems for attack detection, critical components, consumer protection/consumer information
- Sections 4a and 4b: Access to federal IT systems data and evaluation of IT security risk information, including logging data and inventory data
- Section 7a: Examine IT products and systems, requiring manufacturers to provide technical details of products or tell public manufacturers who refused to provide them
- Section 7b: Detect security risks and attack methods jeopardize the networks of federal government, critical infrastructure, digital services, or companies in the special public interest
- Section 7c: Distribute technical commands for and order telecommunications to cleanup specifically named malicious program that undermine availability, integrity, or confidentiality
- Section 7d: Order telemedia services providers to implement technical and organizational measures necessary for protecting against unauthorized access to facilities or disruptions, including external attacks
- Section 8f: Companies in the special public interest must submit IT security self-declarations every two years showing certifications, audit documentation, or how it protect IT systems, components, and processes as well as report disruptions or significant disturbances to IT system, component, or process availability, integrity, authenticity, and confidentiality
- Section 9a: BIS acts as the National Cybersecurity Certification Authority to authorize conformity assessment bodies, audit conformity assessment, inspect conformity assessment bodies’ business premises and offices, revoke cybersecurity certificates issued
- Section 9b: Manufacturers of critical components must submit a declaration of trustworthiness to operators of critical infrastructure, and the Federal Ministry of the Interior, Building and Community may prohibit use is the manufacturer is not considered trustworthy
- Section 9c: Introduce uniform IT security label based on requirements published by BIS to inform consumers about a product’s IT security and usable only if BIS approve it for the product
Business impact of the IT Security Act 2.0
The IT Security Act 2.0 has a few direct and potential impacts, depending on a company’s industry and vertical.
Critical Infrastructure, Federal Agencies, and Companies in the Special Public Interest
Fundamentally, the IT Security Act 2.0 applies to critical infrastructure and government agencies. The BIS’s expanded core tasks now include reviewing covered entity certification and audits, as well engaging in audit functions of its own. While many of these entities already engage in attestations, audits, and certifications, this creates an additional compliance and documentation requirement.
Manufacturers of Critical Components
Manufacturers of critical components need to meet trustworthiness requirements, proving and maintaining their products’ security. If they fail to maintain this, then the government can prohibit the product’s use.
Consumer Technologies
Although not mandatory, the IT security label will likely place additional requirements on companies as consumers begin to use the label when making technology decisions. The IT security label can become a product differentiator, especially in competitive markets.
Centralized Log Management for IT Security Act 2.0 Compliance
Using a centralized log management solution that incorporates security analytics enables you to document your security controls and continuously monitor their effectiveness. Further, entities, like telecommunications companies, that need to clean up systems once BIS sends out notifications, can more rapidly search for the identified malicious programs.
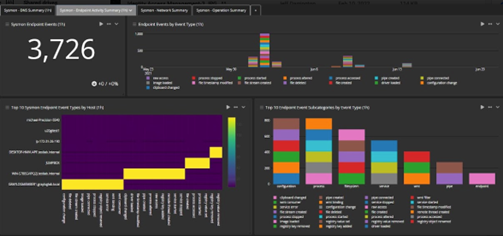
Access Monitoring
Centralized log management solutions ingest access logs from across on-premises and cloud-based resources. With built-in user and entity behavior analytics (UEBA), centralized log management provides a robust access monitoring solution that entities can use to detect and investigate anomalous behavior in complex environments.
Some security functions that centralized log management paired with security analytics can enable include:
- Privileged access management (PAM)
- Password policy compliance
- Abnormal privilege escalation
- Time spent accessing a resource
- Brute force attack detection

Network Monitoring
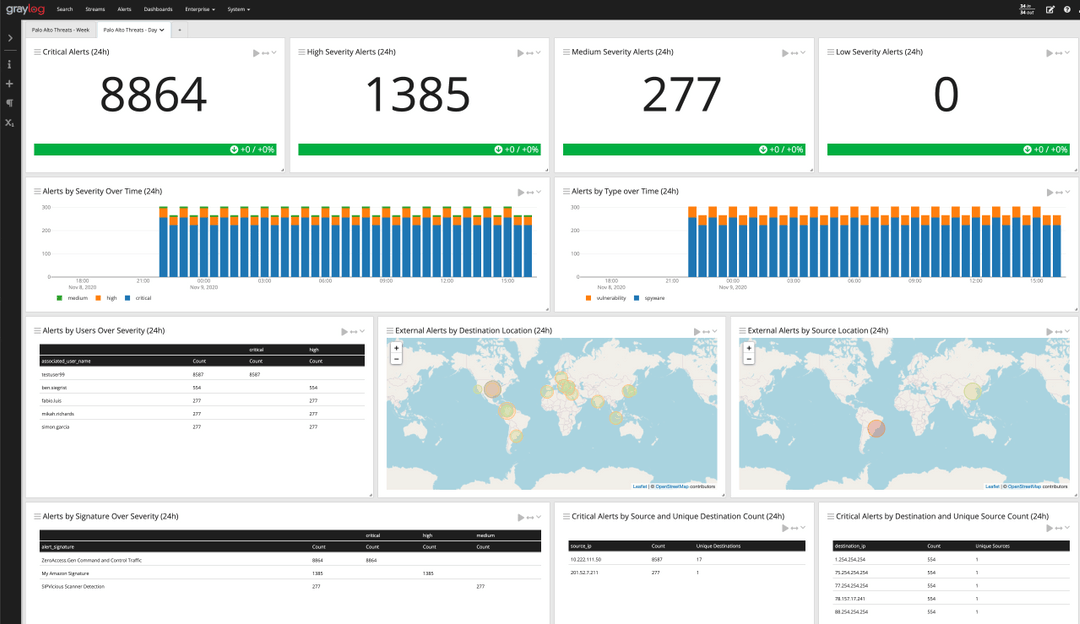
Monitoring network security requires an entity to correlate and analyze data from various solutions. For example, firewalls provide visibility into abnormal inbound and outbound traffic that could signify data traveling to a cybercriminal-controlled server,

With Intrusion Detection Systems (IDS)/Intrusion Prevention Systems (IPS), entities gain visibility into potential evasion techniques for a more complete story.

By setting network traffic baselines and looking for anomalies with the solution’s security analytics, entities gain visibility into potential security incidents.


Data exfiltration
Germany’s Bundestag passed the IT Security Act 2.0 in response to the changing nature of cyber attacks, including double extortion ransomware attacks that include data exfiltration. Using a centralized log management solution with security analytics enables entities to bring together threat intelligence, monitoring dashboards, and high-fidelity alerts for enhanced threat and incident detection.
Aggregating, correlating, and analyzing network monitoring logs, antivirus logs, and UEBA enables entities to gain insight into abnormal data downloads. Further, they can create alerts around these data points for better incident detection.

Incident response and automated threat hunting
A centralized log management solution with lightning fast search capabilities enables robust incident response programs and reduces key metrics like mean time to investigate (MTTI) and mean time to respond (MTTR).
Further, parameterized search queries not only help with investigations because they provide real-time answers, they also enable proactive threat hunting that can help detect advance threat activities like:
- Abnormal user access to sensitive information
- Abnormal time of day and location of access
- High volumes of files accessed
- Higher than normal CPU, memory, or disk utilization
- Higher than normal network traffic

Compliance and post-incident reporting
For compliance purposes, entities need to document their monitoring and post-cleanup activities. A centralized log management solution’s dashboards provide the high-level visualizations that enable entities to evaluate their security monitoring and cleanup activities.
For example, if trying to prove that the entity eradicated the malicious program, a dashboard can show:
- Beginning of incident: when logs documented changes
- Activities during the incident: what types of changes the logs documented to highlight what the threat actor tried to do
- Malicious activity containment/eradication: when logs stop reporting the activities indicating the threat actor is no longer acting in the system
Graylog Security: Security analytics for compliance enablement
Graylog’s security analytics and anomaly detection capabilities provide the cybersecurity platform entities need without the extra features that make complying with the IT Security Act 2.0 more expensive. Using our powerful, lightning-fast features and intuitive interface, entities can lower their labor costs and respond to BIS threat intelligence faster.
With our high-fidelity alerts, entities can reduce alert fatigue while enhancing security across their environments, including their development environments to protect sensitive consumer product code.
Our pre-built content includes search temples, dashboards, correlated alerts, and dynamic lookup tables so that entities can gain immediate value from their logs to accelerate their compliance activities.
For more information about how Graylog Security enables IT Security Act 2.0 compliance, contact us today.