A long time ago, in a SOC far, far away…analysts were drowning in alerts, chasing context across fragmented screens, and watching real threats slip past detection gaps. Today, the Rebellion fights back.
This isn’t a release built around a single marquee feature. It’s the result of our team listening to you on the front lines with an ear for removing the friction that makes your jobs harder than they need to be. Graylog’s R&D team has outdone themselves, and I cannot wait for you to get your hands on what they’ve built.
Let’s walk through it.
A New Hope for Ending Alert Fatigue
If there’s one thing I hear from lean security teams more than anything else, it’s this: “I can’t see the signal through the noise.” Alert fatigue is the dark side of a well-instrumented environment, and the more you monitor, the more you risk burying what matters.
In 7.1, we attacked this problem from multiple angles.
Fundamental in 7.1 is a shift from an event-based triage experience to a case-based methodology.
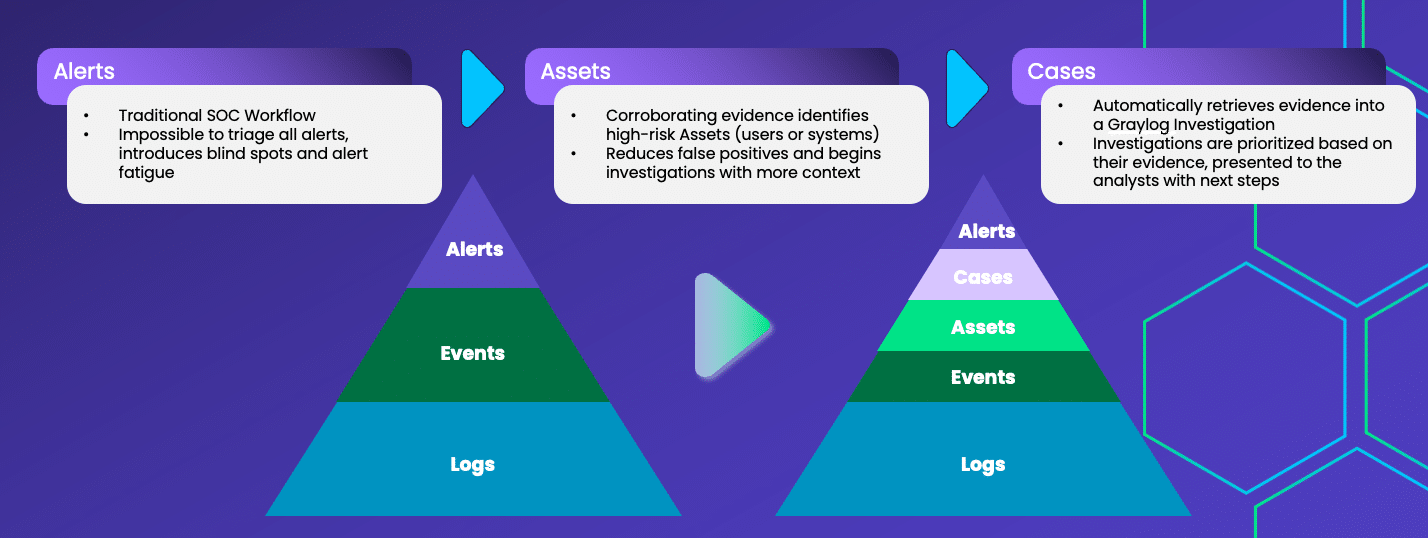
When we triage an individual alert, it’s up to us to capture the context of what happened and connect it to other disparate alerts. This is all before we even know if it is a false positive.
Automatic Investigation Creation creates investigations using your Asset Risk thresholds, with options to nuance risk thresholds by your user and machine groups to effectively capture where your risk appetite differs.
Triage stays on the alert page with an added twist.
7.1’s Slice-By allows you to quickly filter on a column’s values. For example, slice by
- Investigation, sorted by Investigation Priority, to begin analyzing all the events of the investigations Graylog has created for you.
- Asset, sorted by Asset Risk, to see any other assets accumulating a higher risk score prior to hitting its threshold
- Status, sorted by Event Risk, to see if you have any re-occurring events that require tuning.
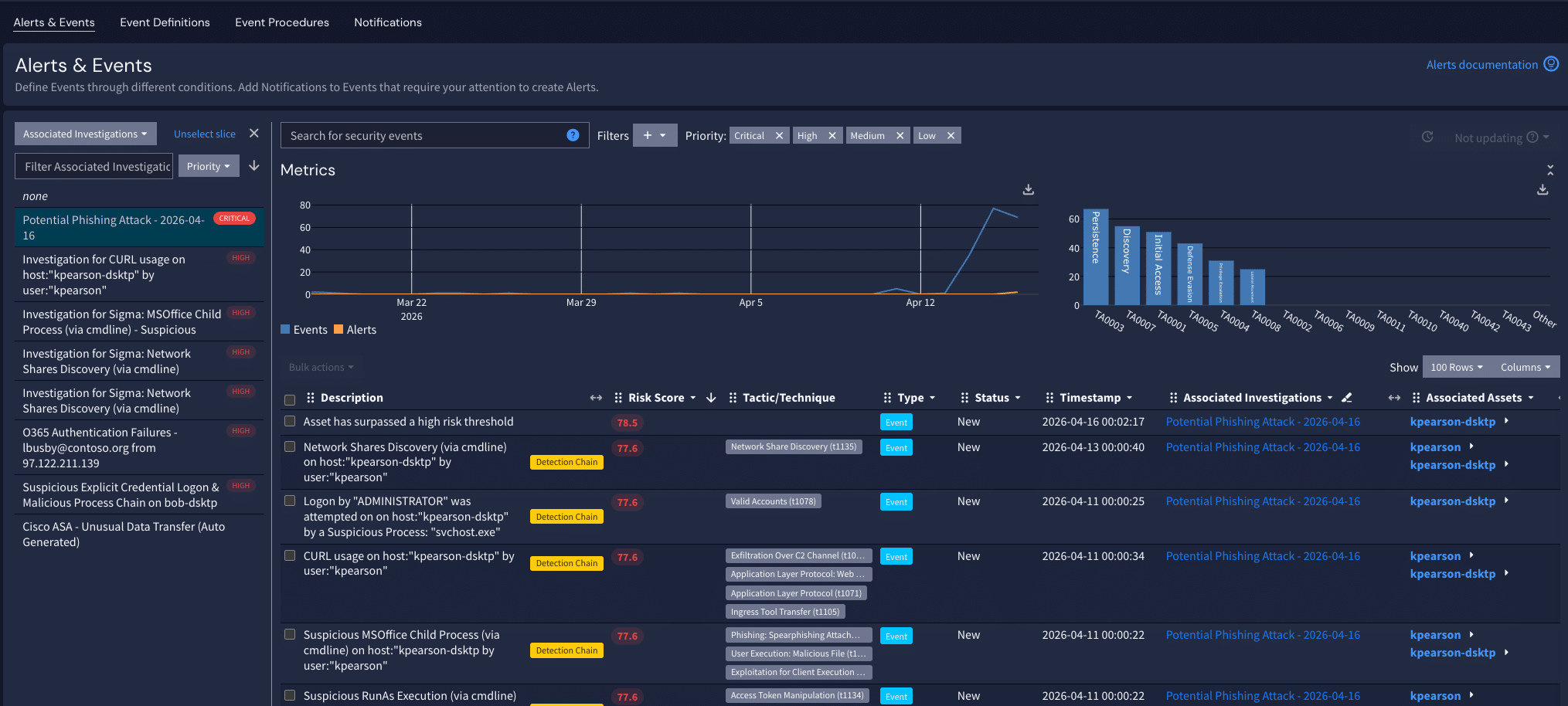
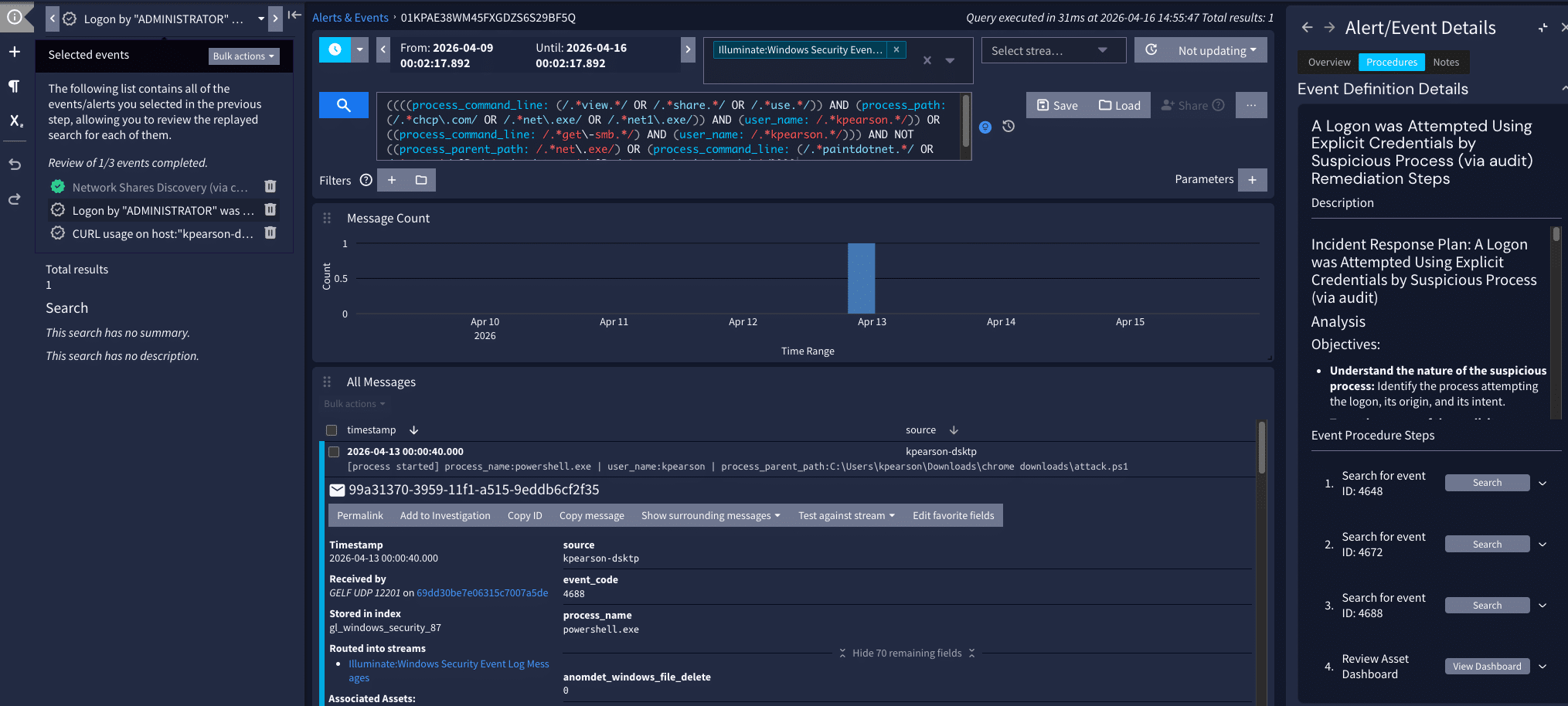
Back to our Investigation that Graylog has created for us, bulk select the events and hit replay.
The Context Sidebar provides details on the event, procedure steps, and associated assets that stay with you as you progress your investigation.
Additional features have been added to reduce the amount of scrolling and clicking needed to wrap up your investigation.
- Event Summary Templates on the Alerts page surfaces key details in the description field, such as the user and system, removing the need to open the Event row to see these details.
- Favorite Fields bubbles up the most vital fields to the top, in any order you specify.
- Bulk Add to Investigation quickly adds all pertinent logs in one foul swoop?
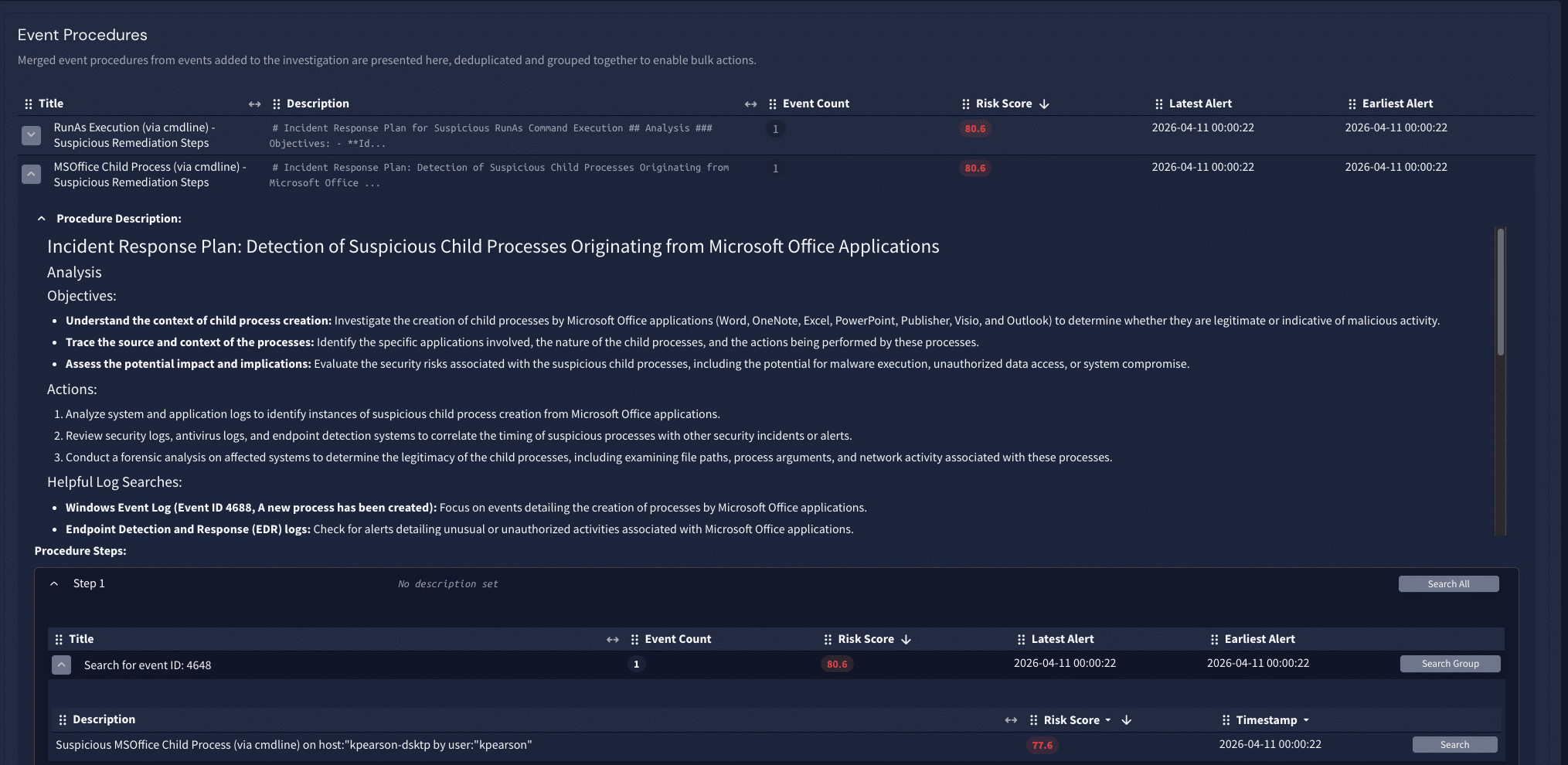
- In the full-page view of the Investigation Merged Event Procedures, displays a deduplicated list of steps and groups similar actions together into a single click.
These aren’t incremental improvements. They combine to provide demonstrable reduction in your detection and response times focused on the areas that represent the highest probability of compromise.
Behavior Analysis Strikes Back
We’ve enhanced Graylog’s Anomaly Detectors with greater flexibility, adding vendor agnostics, more tuning options, and faster resolution time with search replay.
We have also added new baselining techniques for recognizing Impossible Travel and Log Fluctuations.
The Infrastructure That Keeps the Hyperdrive Running
None of the analyst-facing improvements matter if the platform underneath them is slow or fragile. The engineering team has made substantial investments in the data layer in 7.1 that I want to make sure don’t get overlooked.
Dynamic Shard Sizing sets shard counts to their optimal value automatically — this is a meaningful improvement to search performance that many large customers will feel immediately. And Dynamic Shard Count for Restored Index Sets means that data lake restores now scale with the shard count, making retrieval significantly faster.
For administrators managing large environments: MongoDB nodes are now visible on the Cluster Configuration page, and a full Inputs Page Revamp makes managing dozens of Inputs and Forwarder Input manageable.
We also added License Usage Alerts, so you will never be surprised by where you stand against your ingest limits.
This is the hyperspace jump your infrastructure didn’t know it needed.
Thank You to the Rebel Alliance
None of this happens without an incredible R&D team that shipped across five themes simultaneously, analyst experience, threat detection, platform administration, infrastructure performance, and AI foundations, while also smashing bugs to keep the lights on for 60,000+ organizations across 180 countries.
Graylog 7.1 is available today. Check out the release notes here. May the Fourth be with you — and may your alert queues be short, your detections sharp, and your investigations swift.

Seth Goldhammer is VP of Product at Graylog. Graylog 7.1 is available now for Enterprise, Security, and Open users. Visit graylog.org to upgrade or get started.