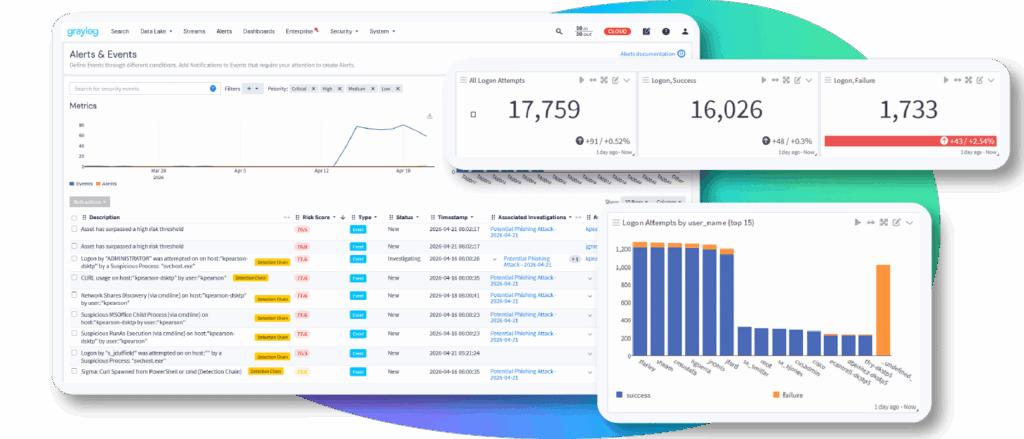




















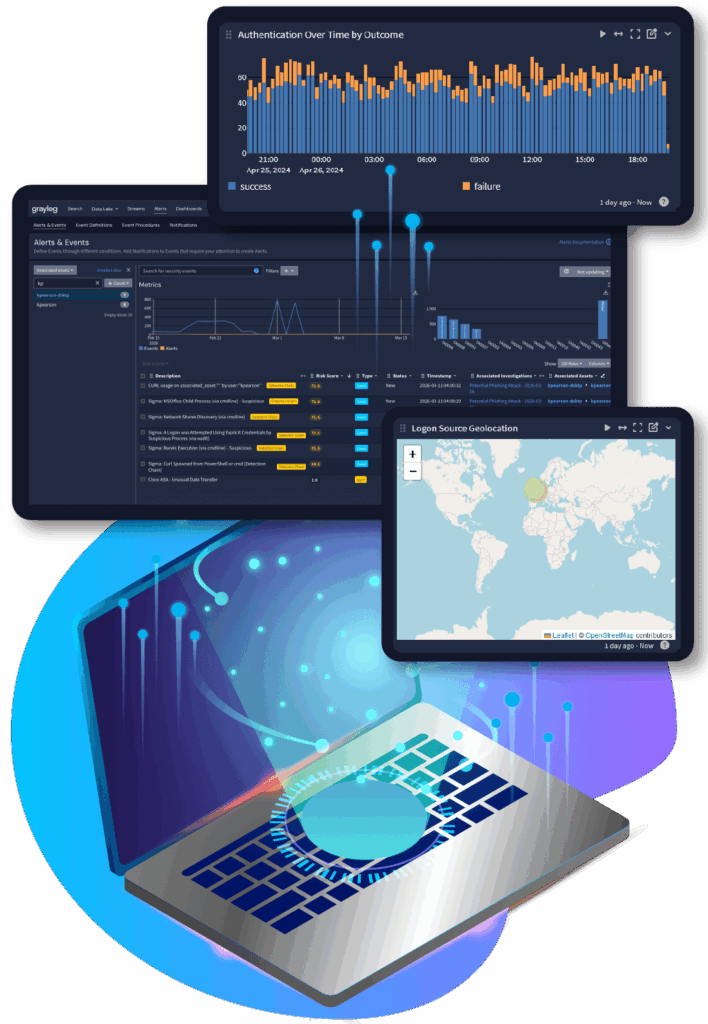
Detect high-risk threats. Automate investigations. Store everything—without spiking your license costs. Graylog gives you real-time defense with long-term visibility.
Route logs your way. Analyze across platforms. Keep control over your architecture and your budget. Graylog lets you run lean, powerful, and on your terms.
Other platforms make you bolt on tools to manage log routing, data tiers, and storage costs. Graylog bakes it in. Preview archived data, route logs, and restore only what you need. All without paying to ingest or buying another license.

Whether you’re just curious or comparing platforms, our demo is a good place to start.