Security Operations
Navigating the Digital Minefield
In today’s hyper-connected digital landscape, organizations face a monumental challenge: safeguarding their assets and data against an ever-evolving tapestry of cyber threats. As business operations grow more intricate and intertwined, gaps in security posture can lead to grave consequences, including irreparable security breaches, financial losses, reputational damage, and operational disruptions.

Let Graylog Drive Security Operations While You Relax in the Passenger Seat
Graylog offers tailor-made solutions to help you overcome your security operations challenges of today and tomorrow.
Log Collection
Normalization, Correlation, & Contextualization
Threat Detection
Alerting
Incident Investigation
Incident Response and Recovery
Reporting
Harness the Power of Graylog Security
Graylog Security is a linchpin in the drive toward achieving and maintaining audit & regulatory compliance. By aggregating and analyzing data from various sources, Graylog Security offers:
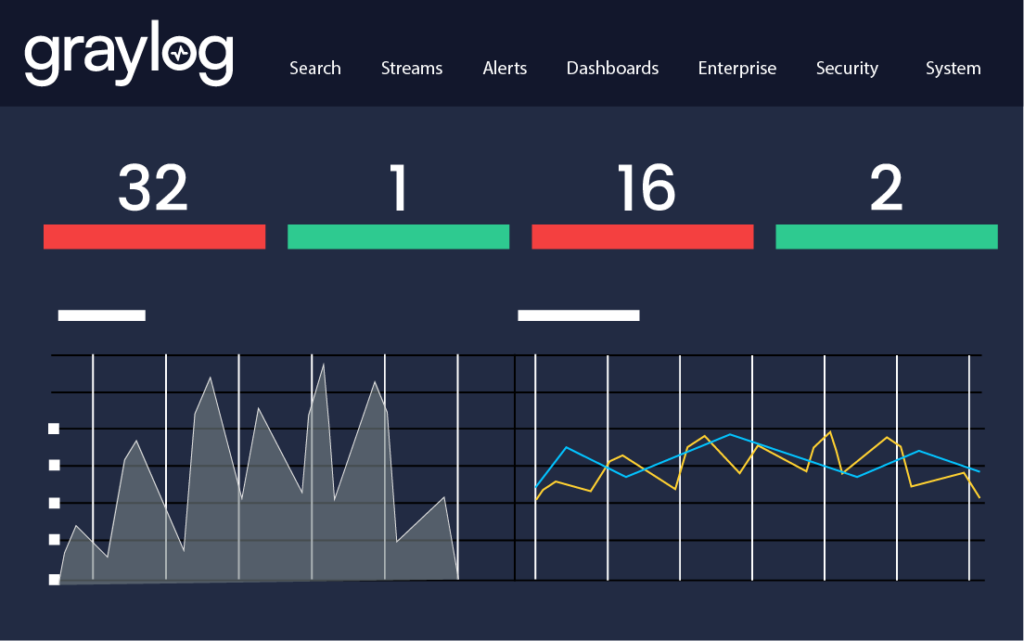
Real-Time Threat Detection
With an array of analytical techniques, including correlation, advanced statistical analysis, and anomaly detection, Graylog Security detects security concerns and calculates the risk for each alert, enabling your security teams to act before damage is done.

Enhanced Compliance Management
Graylog Security can simplify regulatory compliance by providing unified reporting and audit-ready insights, reducing the risk of violations and associated penalties.
"Best SIEM and log aggregation tool available right now: The amount of flexibility and insight into logs and operations provided by it are astounding."
- System Administrator in the IT Services Industry
The Imperative of Graylog API Security
In the age of continuous digital transformation, Application Programming Interfaces (APIs) have become the bedrock of enterprise integration. However, they also introduce new vectors for attacks. Graylog API Security can help you by providing the following:
Granular Access Control
Fine-tuned permissions ensure only legitimate users and systems interact with your APIs, preventing unauthorized data access or manipulations.

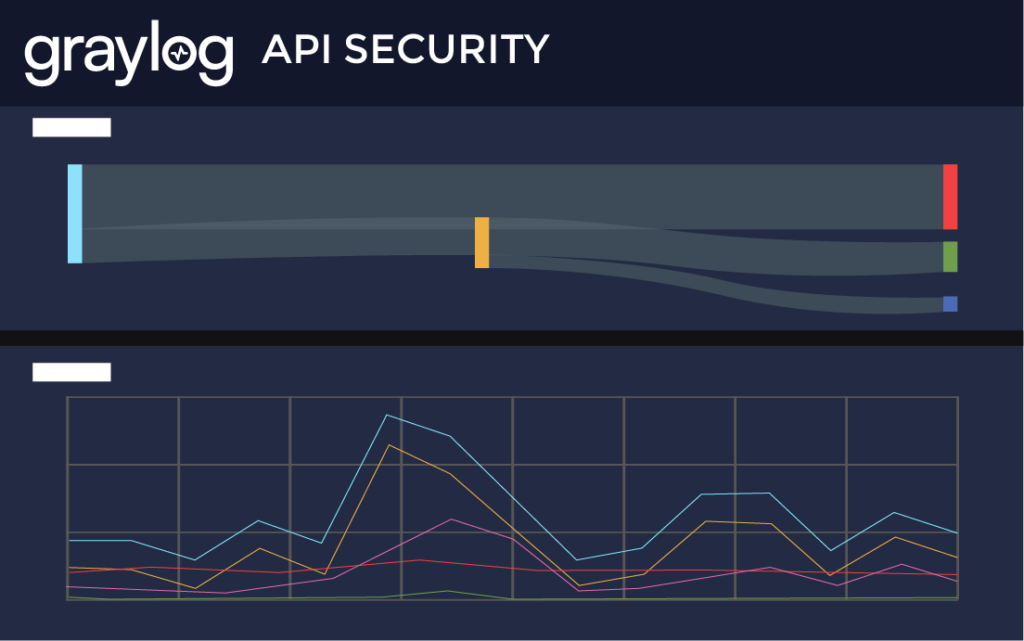
Continuous Vulnerability Monitoring
By constantly scanning and evaluating API calls, Graylog API Security can identify and block malicious attempts, safeguarding the integrity of your digital services.
A Synergistic Approach: Graylog Security + Graylog API Security
Combining Graylog Security with Graylog API Security creates a powerhouse of protection. The holistic combination amplifies the capabilities of each solution, giving you:
Comprehensive Visibility
Combining data from Graylog Security and Graylog API Security gives your security teams a bird’s-eye view of your entire security landscape, illuminating hidden risks and potential attack paths.

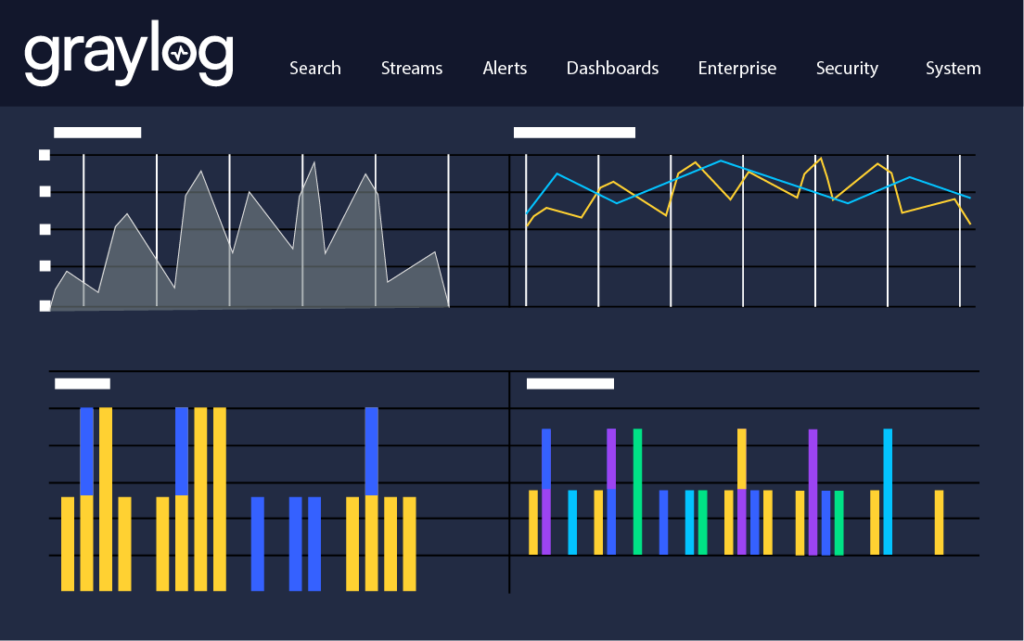
Informed Incident Response
Leveraging insights from both realms, organizations can implement well-informed responses to detected threats, ensuring rapid containment and minimal damage.
Ready to Rise Above the Challenge?
The complexities of modern cyber threats necessitate robust and multi-faceted defense mechanisms. By implementing both Graylog Security and Graylog API Security, you can address the individual challenges posed by internal and external threats and craft a fortified, synergistic shield against the myriad of cyber risks lurking in the digital shadows. Our solutions represent the future of proactive, intelligent, and resilient security operations.
Resources
Security Operations (SecOps)
Read Articles About Security Operations:
Learn More About Security Operations (Sec Ops)
Security Operations (SecOps) refers to a collaorative approach that combines security and IT operations efforts to focus on monitoring and assessing risk, protecting corporate assets, and often operates from a security operations center (SOC). Graylog Security is designed to prevent silos within the wider IT organization by helping SecOps focused organizations achieve their security objectives without compromising IT performance.
Some of the key roles on a SecOps team include incident responders, security investigators, advanced security analysts, SOC managers, and security engineers/architects. These roles cover a range of cybersecurity threats and attacks, ensuring a cohesive and effective defense against cyber threats.
While SecOps focuses on the collaboration between IT security and operations teams, DevSecOps is an extension of DevOps that integrates security practices into the software development lifecycle (SDLC). DevSecOps emphasizes collaboration between development, operations, and security teams to create more secure applications from the ground up, ensuring security measures are implemented throughout the DevSecOps lifecycle.
Automation and AI tools are increasingly integrated into SecOps for functions such as incident detection, response, and analysis. These tools enable SecOps teams to mine data, assign risk scores, cluster commonalities, differentiate threats, and recommend remediation steps. Automation enhances the security operations platform by providing insights that improve detection and prevention, while freeing up human resources for strategic SecOps tasks.
Other Use Cases
Ready to View Plans?
Get the Monthly Tech Blog Roundup
Subscribe to the latest in log management, security, and all things Graylog blog delivered to your inbox once a month.


