Anomalous behavior analytics is one of the many advantages that big data analytics brings to the table. What role does log monitoring have in this process, and how does it work together with behavioral analytics?
Behavior analytics is a powerful tool in intrusion detection and prevention, using typical user behavior insights to detect suspicious activity. What role does log monitoring have in this process, and how does it work together with behavioral analytics?
WHAT IS BEHAVIORAL ANALYTICS?
User behavior analysis (UBA) is the cybersecurity process of detecting insider threats, targeted attacks, and financial fraud. How does UBA work? It analyzes human behavior based on a large data sample and uses analytics to detect behavior patterns. Any behavior that differs from the pattern signals a potential threat, which the person in charge of IT security should address right away. One of the critical aspects of incident response is the response time. If you don’t react quickly enough, the intruder can steal or damage your data and disrupt your organization’s operations.
Prevention is a more efficient and more affordable option than troubleshooting. This is why it is crucial to invest in a tool that helps utilize the insights gained from anomalous behavior analytics in the fastest and most meaningful way. Log monitoring tools are a great way to speed up and automate incident response either by providing behavioral analytics as one of the features or by easily integrating with another analytics tool.
HOW CAN LOG MANAGEMENT ENHANCE BEHAVIORAL ANALYTICS?
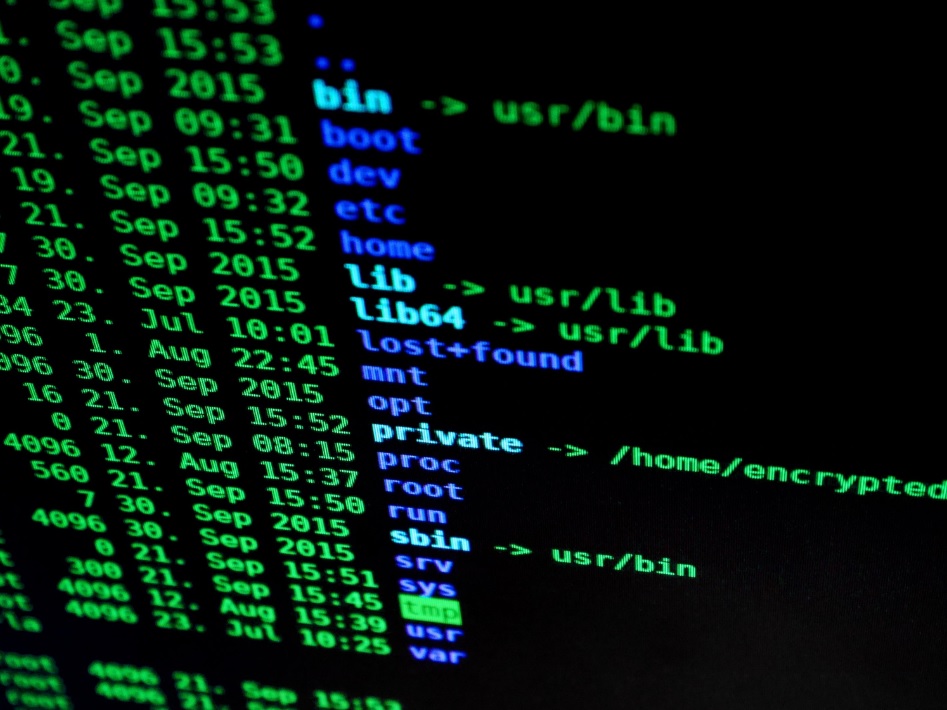
Let’s take a step back and talk about big data. With data science on the rise, we keep hearing about machine learning, AI, and big data, but what does it have to do with log management? Big data refers to large data sets – just like those stored in a large number of log files. It is hard to analyze big data using traditional methods because of its size. This is why a large part of data science is dedicated to big data analysis.
The data stored in logs is a potential gold mine of information. If processed correctly, this data can tell you the weak points of your environment so you can improve overall security. It can help you make business decisions and learn more about your customers, and it can also predict how those customers will act in future interactions. But for this to prove successful, you need two things – quality data and quality analysis. We can safely assume that behavioral analytics is the type of quality analysis we need. But what about the data?
The importance of log management lies in providing quality data. First of all, log management ensures a centralized approach – collecting logs from different sources into one place. Secondly, for you to analyze data, it needs to come in a uniform format. Initially, this was not the case. For example, router logs look differently than system logs. A log management tool takes care of this with a unified format. In the case of Graylog, logs are stored in Graylog Extended Log Format (GELF).
USING LOG MONITORING AND BEHAVIOR ANALYTICS TO IMPROVE CYBERSECURITY
As mentioned before, user behavior analysis determines typical user behavior. Every action that stands out from this pattern signals a potential threat. By detecting a suspicious activity as soon as it happens, log monitoring helps detect threats and attacks before they occur. Most log management software offers several ways to keep you alert – via mobile phone, desktop notifications, or email.
There are five phases of intrusion in every cyber attack: reconnaissance, initial exploitation, establish persistence, move laterally, collect, exfil, and exploit. There are different security strategies for each stage, depending on how far the attacker has penetrated. To learn more about how to use log management software, read our post on Cybersecurity: Understanding the 5 Phases of Intrusion.
In case that, despite monitoring, a security breach occurs, early detection provides better damage control. If your IT environment has been rendered non-operational, early detection helps decrease downtime by letting you take action as soon as possible and restore the system. This is especially important if you provide a service where significant downtime may lead to high customer churn. Also, log management shouldn’t be limited to computers. There are more and more cyber attacks on IoT devices because they are very vulnerable to hackers. If your environment has IoT devices, you can read our blog post on improving IoT security with log management.
Anomalous behavior analytics is one of the many advantages that big data analytics brings to the table. It is growing more reliable and effective with data science development, which is why you should consider getting a quality log monitoring and data analysis tool.