Why Audit Readiness Accelerates Revenue
At 3am, you wake up in a cold sweat from a nightmare. The dream? You showed up to test for your most difficult class without having studied. Unprepared, your dream self sat in an uncomfortable desk, staring at a piece of paper and panicking. In the corporate world, an audit can induce the same sense […]
The Four Environments Where SaaS-Only SIEM Fails

Picture a cybersecurity team responsible for protecting a classified military installation in a remote operational theater. No internet connection. No cloud services. Classified and unclassified networks running on physically separate infrastructure. Their security information and event management system has to detect threats, correlate events, and generate alerts with zero external connectivity, for the entire deployment. […]
How to Build a Cost-Effective Log Retention Strategy

Nearly every home has that drawer or doom corner where you store all those items that you don’t need every day but that you still want to keep for those “just in case moments.” If you’re a document connoisseur, you may have financial documents that go back years because an accountant once warned you that […]
Graylog Recognized by Users in the 2026 Gartner®️ SIEM VOC
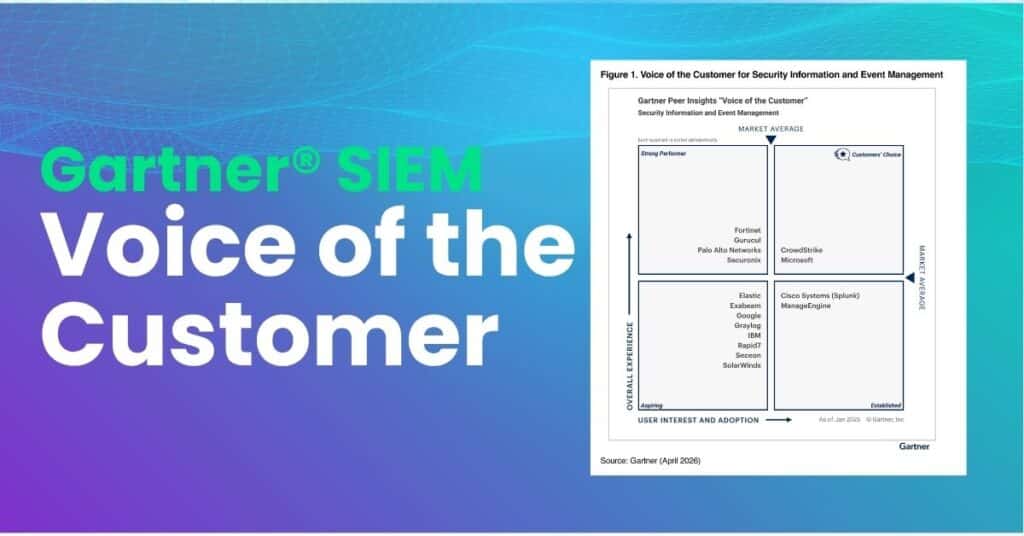
Key Points Graylog received an overall rating of 4.6 out of 5.0 in the 2026 Gartner® Peer Insights SIEM Voice of the Customer report 86%* of verified enterprise reviewers said they would recommend Graylog to a peer or colleague *Based on 52 reviews as of Jan 2026 Ratings of 4.4 or higher across every category […]
15 Risky Cloud Misconfigurations and How To Mitigate Them

When people start driving, one of the first things they learn is how to set the rear-view and side-view mirrors. Whether driving locally or on the highway, these mirror configurations reduce accident risk because they improve the driver’s visibility into the cars behind and around them. In the cloud, various technical configurations act similarly. Cloud […]
What’s New In Graylog 7.1 Webinar

What to Expect? Graylog 7.1 is built for lean security and IT operations teams who need real outcomes, not more tools, more add-ons, or more manual work. This 30-minute deep dive session covers what’s new and what it means for your team. When? Tue, May 19, 2026 11:00 AM EDT What you’ll learn: How […]
Critical Windows Event ID’s to Monitor
Like most organizations, your company likely invested in various Microsoft products. The Microsoft ecosystem provides businesses with nearly every kind of technology necessary, from workstation operating systems to Azure to Windows 365 that includes cloud-native versions of their traditional Office tools and the communication platform Teams. However, attackers are just as invested in the Microsoft […]
India’s Data Protection Law: The Digital Personal Data Protection Act

In 2023, India’s Parliament approved and published The Digital Personal Data Protection Act (DPDPA). In many ways, the DPDPA is similar to other regulations, like the General Data Protection Regulation (GDPR). It establishes a similar data subject, or in this case Data Principal, rights of notice, consents, access, correction, and erasure. In other ways, the […]
Understanding the Australian Information Security Manual (ISM)

The Essential Eight identifies the most critical cybersecurity risk mitigation controls, providing a set of minimum baseline strategies. As organizations work to mature the security posture, the Essential Eight maturity model offers some options that they can use. However, for organizations that need to implement a more comprehensive security program, the Australian Signals Directorate (ASD) […]
May the Logs Be With You: Graylog 7.1 Is Here

A long time ago, in a SOC far, far away…analysts were drowning in alerts, chasing context across fragmented screens, and watching real threats slip past detection gaps. Today, the Rebellion fights back. This isn’t a release built around a single marquee feature. It’s the result of our team listening to you on the front lines […]
40 Infosec Metrics Organizations Should Track
In today’s data-driven world, CISOs and senior leadership need to prove that their security programs mitigate risk. Just like grades theoretically quantify how well students understand material their teachers present, cybersecurity metrics quantify your security controls’ effectiveness. As the threat landscape becomes more complex, security teams struggle to identify the metrics that best showcase their […]
An Introduction to the NIST Risk Management Framework (RMF)
While inherently critical to today’s businesses that run on data, implementing and enforcing data security and privacy has never been straightforward. Between collecting different types of sensitive data and deploying unique architectures, organizations cannot adopt a one-size-fits-all solution, meaning that every security architecture is unique. With no absolutes around how to build security into the […]
