For logs and tracking insider threats, you need to start with the relevant data. In these turbulent times, IT teams leverage centralized log management solutions for making decisions. As the challenges change, the way you’re monitoring logs for insider threats needs to change too.
WHY DO INSIDER THREATS MATTER DURING TURBULENT TIMES?
Furloughs, workforce reductions, and business practice changes as part of the COVID stay-at-home mandates impacted IT teams. Not only did they have fewer resources, but they also needed to monitor increasingly complex Identity and Access Management (IAM) activities.
Distributed workforces made visibility into how users access resources and what they do with the access hard to manage. Add in the economic and physical health insecurities, and you have a recipe for disaster.
Bad actors pay attention to social media, watching for employment status changes on LinkedIn. They’re looking for accounts with elevated privileges, so they can leverage that access to gain a foothold. Ultimately, they hope to deploy a ransomware attack or exfiltrate data to sell on the black market.
Some heightened insider risks include:
- Successful phishing attacks
- Credential theft
- Fraud
With people distracted and stressed out, they’re less likely to be focused on security. Being preoccupied makes them easier phishing targets. They’re also more likely to be concerned about money. Financial pressures can lead to financial fraud.
This perfect storm means focusing on insider threats more diligently.
PLAN THE DATA YOU WANT TO COLLECT
For tracking insider threats with logs, you need to know and focus on the relevant data specifically. To monitor for malicious activity with log data, you need to collect the right user activities, access logging data, and network monitoring information to detect a new risk.
Various data elements that you should consider collecting and using for risk decisions data from:
- Applications, operating systems, and devices
- User accounts
- Access controls
- System Information and Event Management Systems (SIEMs)
- Security Orchestration, Automation, and Response (SOAR) tools
- Intrusion Detection Systems (IDS)
- Intrusion Protection Systems (IPS)
- Endpoint management tools
- Endpoint protection systems
- Firewall and VPN access
- User and Entity Behavior Analytics (UEBA)
With all this data, you need a centralized location that can help you collect and evaluate it. Graylog’s native connectors make it easy to aggregate data from your environment, regardless of source. This way, you can collect and organize real-time employee monitoring information to enhance your threat management and incident response activities.
SET THE RIGHT ALERTS
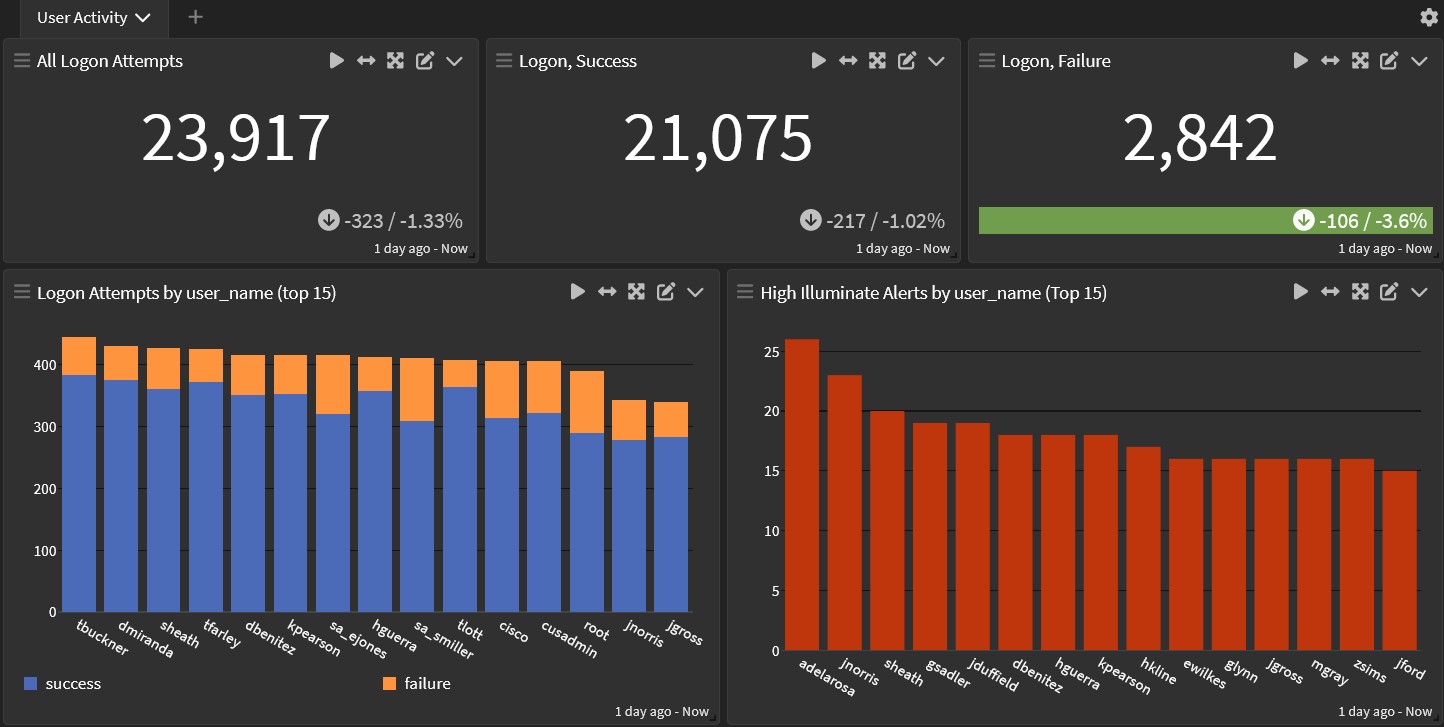
Centralized log management makes it easier to see data with things like dashboards and visualizations. To use these effectively, you need to be watching them regularly. The real value to insider threat detection lies in alerting capabilities.
Once you know the data that matters to your environment, you need to know the alerts that will help you respond. Alerting is the pivot point for security analysts. They give visibility into what new risks impact the environment, so you know what to needs attention.
With Graylog, security professionals can use two additional features to enhance their insider threat monitoring processes.
DYNAMIC LISTS
Custom dynamic lists combine alert parameters with lookup tables. This helps alleviate alert fatigue when you connect multiple security tools and data sources. The dynamic lists automatically update when the parameters you set update. With this functionality, you can create more specific alerts around real risks to your environment.
Security professionals might dismiss the value lookup tables bring to their research. In dynamic IT stacks, the data that the tables use needs to be updated regularly to keep them fresh.
EXAMPLE
Consider the use case where a bad actor wants to use an orphan account to get into your systems. This can be either a former employee or a cybercriminal. You need to know if anyone tries to use these credentials after they should have been terminated. This list is going to change regularly, though.
You can define a parameter using a list of former employees. Then add in access behaviors and authentication behaviors to compare against anyone on that list. Triggering alerts for any SSH would be too much.
If you have a dynamic list of former employees that updates when your Active Directory or HR system updates. You have a very explicit risk if someone attempts to SSH with those credentials.
CORRELATION ENGINE
The correlation engine lets you find patterns in the data. You can take a single event and leverage multiple fields with that event to correlate data. You can also take data from across multiple events in order to correlate an alert outside of multiple sources.
Correlation rules are simple to use by creating the same search criteria across dashboards. Then you filter and code data at the search window. In order to build successful outputs, you can use some of the built-in correlation rules. Doing this can better define correlation events in your environment.
EXAMPLE
Consider a use case where somebody leverages escalated privileges in Linux. Then while leveraging that privilege, they also create a user. Getting notified about this would be the first step in responding to a potential attack.
Another use case is someone logging in as a service and trying to clear the event log. If your policy allows a service account to do this, then the activity would go forward. Individually, neither of these activities might trigger an alert. However, by using the correlation engine, you create a high-fidelity alert output that requires a response.
GRAYLOG: CENTRALIZED LOG MONITORING FOR INSIDER THREATS
Insider threats are a major concern for every organization. With a centralized log management solution, you can collect, aggregate, and correlate data from various sources. This reduces insider threats in your environment and creates an audit trail.
However, to effectively detect potential security events in your environment, you need to create high-fidelity alerts. Casting too wide a net leaves your security professional suffering from alert fatigue. Too narrow a parameter means you might miss an important activity or pattern. With Graylog, you can set precise parameters by correlating data and leveraging dynamic lists to strike the right security balance.