It’s mid-morning. You’re scanning the daily news while enjoying a coffee break. You come across yet another headline broadcasting a supply chain data breach. Your heart skips a quick, almost undetectable, beat. You have the technology in the headline in your stack. You set aside your coffee and begin furiously scanning through the overwhelming number of alerts triggered across all your technologies. The alerts you ignored because you figured most were false positives, and you were too busy to look through all of them anyway. Now, you have to investigate each and every one of them, hopefully before your boss calls and asks, “Are we vulnerable?”.
As your organization adopts new technologies, your attack surface grows. You know that you need to implement a cybersecurity risk management program and strategy. Saying you need one and implementing one are two different things. A cybersecurity risk management program that includes multiple departments helps you understand and mitigate risk more efficiently and effectively.
WHAT IS RISK AND RISK MANAGEMENT IN CYBERSECURITY?
Risk is the potential business impact if malicious actors find a way to gain access to your systems and networks. Some examples of cybersecurity risks might include:
- Phishing attacks
- Ransomware
- Misconfigurations
- Excess user access
You might already know the risks and have an as-needed approach to mitigating them. The problem is that this isn’t risk management.
Risk management is a strategic set of processes that identify, analyze, and assess the potential business impact a security incident can have. You create proactive, repeatable steps for detecting, investigating, and responding to incidents with risk management.
CREATE A CROSS-DEPARTMENTAL RISK MANAGEMENT TEAM
Although many daily cybersecurity tasks fall to IT or security teams, you don’t have to do all the work alone. If you are doing the work alone, then you might not have a strong security risk management program.
If you’re looking at your networks and systems, you already know that technology touches every part of the business. Simultaneously, while you’re an IT or security person, you may not – and probably don’t want to – know the ins and outs of every part of the business.
OPERATIONS
Operations monitor your technology all day long. Their goal is to maintain service uptime to meet service level agreements. They’re the ones doing the help desk intake that can lead to discovering a security incident. They know what “normal” network traffic and application activity looks like. Talking to them can help set baselines.
EXAMPLE
A distributed denial of service (DDoS) attack leads to system downtime, but the tickets just say that the service is unavailable.
COMPLIANCE
The person in charge of managing compliance can give you visibility into the legal and industry requirements for security. Depending on what your business does, you may need to certify to a standard or meet a legal requirement.
EXAMPLE
You probably need to comply with the Payment Card Industry Data Security Standard (PCI DSS) if you’re accepting credit card payments for services or products.
DEVOPS
Your developers build your applications, your internal applications, or the software you sell. They know the code repositories they used, and they should be engaging in code reviews. By working with them, you’ll learn more about the potential risks and their ability to mitigate them.
EXAMPLE
Code vulnerabilities, like Log4J, have long-range and long-term security impacts. Knowing the code libraries and being able to trace exploitability is one way to help mitigate risks.
DEPARTMENT MANAGERS
Your department managers know what applications they need, why they need them, and who needs access to them. Even if they’re not technical, they can help you better understand how to set mitigating controls.
Example
The head of sales knows who should have access to the Customer Relationship Management (CRM) system and what type of access each person needs. This knowledge can help limit access according to the principle of least privilege.
WHAT ARE SECURITY ANALYTICS?
Security analytics tools give you data that correlates threats with behavior analytics, like network traffic or user behavior. By combining threat intelligence with data analytics, like machine learning, these tools give you a way to detect threats faster.
Some use cases include:
- Insider threat detection
- Malware beaconing
- Data exfiltration
- Compromised credentials
For example, security analytics for malware detection might look like this:


HOW TO USE SECURITY ANALYTICS FOR CYBERSECURITY RISK MANAGEMENT
Managing cybersecurity risk is complex, but at the base, it’s about creating effective processes for detecting, investigating, and resolving incidents. Security analytics provide the data to support your goals so that you can create repeatable, efficient processes.
ADDITIONAL DATA POINTS
Security analytics starts with data. If you have a cross-functional team informing your security risk management program, you can meaningfully incorporate this input. The more data you have, the better the analytics.
Using security analytics allows you to span the diverse risks addressed by the various stakeholders for a broader picture and more robust program.
THREAT HUNTING
With security analytics, you can bring threat intelligence into your daily activities. This supports proactive threat hunting, which is looking for Indicators of Compromise (IoC) to determine whether malicious actors are already hiding in your systems and networks.
With threat hunting, you have a repeatable process allowing you to actively look for compromise instead of waiting for an alert to trigger.
For example, incorporating threat intelligence could look like this:

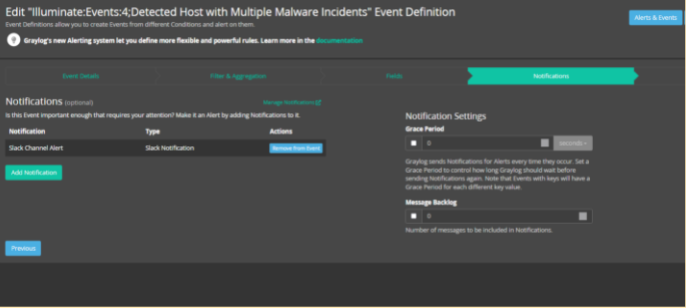
HIGH-FIDELITY ALERTS
With cloud-based environments, you need better visibility into how people are using their credentials. If you’re using security analytics, you can create alerts that make it easier to detect whether a password reset is a real request or an attempted credential-based attack. The machine learning tools can also help mitigate insider threat risks, like someone downloading sensitive corporate information.
High-fidelity alerts reduce the time it takes to detect a security incident, ultimately mitigating risk.



INVESTIGATION
With security analytics enabling high-fidelity alerts, you’re detecting more rapidly, but you’re also investigating the incident’s root cause faster. High-fidelity alerts correlate more information which helps you narrow down your investigation starting point faster.
When investigations are faster, you can limit the impact a security incident has by containing malicious actors and recovering faster.
For example, customizing search and analysis across structured and unstructured event logs can help you pinpoint the source of an issue to more rapidly determine whether it’s a security incident or not:

GRAYLOG: CENTRALIZED LOG MANAGEMENT FOR CYBERSECURITY RISK MANAGEMENT
Graylog’s centralized log management solution gives you the data and visualizations you need to create high-fidelity alerts and the lightning-fast speed necessary for investigations. Graylog gives you the security data needed to start operationalizing your cybersecurity risk management by collecting, aggregating, correlating, and analyzing events across your environment.